This text is machine-read, and may contain errors. Check the original document to verify accuracy.
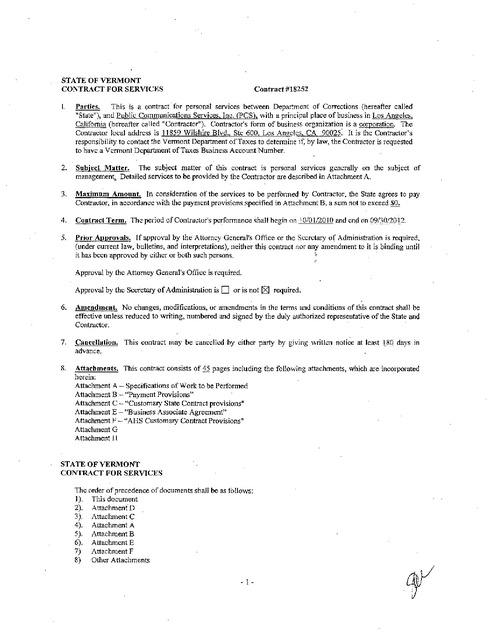
STATE OF VERMONT
CONTRACT FOR SERVICES
Contract #18252
I.
Parties.
This is a contract for personal services between Department- of Corrections (hereafter called
"State"), and Public Communications Services. Inc. (peS), with a principal place of business in Los Angeles.
California (hereafter called "Contractor"). Contractor's form of business organization is a corporation. The
Contractor local address is 11859 Wilshire Blvd., Ste 600, Los Angeles, CA 90025: It is the Contractor's
responsibility to contact the Vermont Department of Taxes to detennine if, by law, the Contractor is requested
to have a VemlOnt Department of Taxes Business Account Number.
2.
Subject Matter. The subject matter of this contract is personal services generally on the subject of
management.,. Detailed services to be provided by the Contractor are described in Attachment A.
3.
Maximum Amount. In consideration of the services to be perfonned by Contractor, the State agrees to pay
Contractor, in accordance with the payment provisions specified in Attachment B, a sum not to exceed $0.
4.
Contract Term. The period of Contractor's perfonnance shall begin on 1010 1120J 0 and end on 09/30/2012.
5.
Prior Approvals. If-approval by the Attorney Generalis Office or the Secretary of Administration is required,
(under current law, bulletins, and interpretations), neither this contract nor any amendment to it is binding until
it has been approved by either or both such persons.
Approval by the Attorney Generatts Office is required.
Approval by the Secretary of Administration is
0
or is not [:><;] required.
6.
Amendment. No changes, modifications, or amendments in the terms and conditions of this contract shall be
effective unless reduced to writing, numbered and signed by the duly authorized representative of the State and
Contractor.
7.
Cancellation. This contract may be cancelled by either party by giving written notice at least llQ days in
advance.
8.
Attachments. This contract consists of 45 pages including the following attachments, which are incorporated
herein:
Attachment A - Specifications of Work to be Performed
Attachment B - "Payment Provisions"
Attachment C - "Customary State Contract provisions"
Attachment E - "Business Associate Agreement"
Attachment F - "AHS Customary Contract Provisions"
Attachment G
Attachment H
STATE OF VERMONT
CONTRACT FOR SERVICES
The order of precedence of documents shall be as follows:
]). This document
2). Attachment D
3). Attachment C
4). Attachment A
5). Attachment B
6). Attachment E
7) Attachment F
8) Other Attachments
. 1-
�WE THE UNDERSIGNED PARTIES AGREE TO BE BOUND BY THIS CONTRACf.
RMONT:
BY THE CONTRACTOR:
DM<
Sign~
!!:£o ~
~
Name: Tommie E. Joe
Agency/Dept.:
Agency of Human Services
Department of Corrections
Title: President & Chief Operating Officer
Address: 1 I 859 Wilshire Blvd .. Ste 600.
Los Angeles, CA 90025
Phone: 800-350-1000 ext. 3037
IOe, @+lJU.~
E-mail:imnmie.-.,
Alternative Contact: (ii'any)·
Revised AHS 712I108
- 2-
I· "
am.c.
�STATE OF VERMONT
CONTRACT FOR SERVICES
ATTACHMENT A
SPECIFICATIONS OF WORK TO BE PERFORMED
The State acknowledges Contractor is subcontracting for the inmate commissary services as well as "the inmate accounting
system and support services to Keefe Commissary Network. However, the Contractor so named in this contract is
ultimately responsible for satisfying, in full, the scope of services and performance expectations as defined within this
contract. Any change in subcontractors must receive prior approval by the State.
Contractor shall designate a project manager, whom shall be approved by the State, as the sole point of contact for all
implementation and deployment activities. Contractor project manager will he responsible for developing and maintaining
the project plan according to accepted best practices project management methodology. Contractor project manager shall
collaborate with a State-designated project manager on all project-related issues including development, review, approval,
and change management of the project plan.,Contractor project manager shall provide the State project manager with at
least weekly status reports, as well as immediate notification of any critical issues as they arise.
Contractor agrees the workstations and associated infrastructure shall become the property of the State at the expiratioq,
cancellation or termination of this contract. All records, documentation, reports, data, etc. obtained through the course of
satislYing the terms of this contract are the exclusive property of the State and shall be provided on demand in a mutually
agreed upon format at no cost to the State.
Contractor will provide the following services for the State:
1. SCOPE OF WORK - INMATE TELEPHONE SERVICES (ITS)
1.1
Contractor Responsibilities - General
1.1.1 Contractor shall comply with all applicable laws, rules, regulations, and orders of any authorized agency,
commission, unit of the federal, state, county or municipal government at no cost to the State. Contractor shall be
authorized by the appropriate governing body and/or regulatory agency to provide the sought after services and
systems. The ITS shall comply with all Federal Communication and/or Utility Commissions regulations.
1.1.2 Contractor must provide the Vermont Public Service Board a list of rates for approval.
J.J.3 Contractor shall furnish evidence oftl>e ownership of the software and/or the ability ofthe firm to license use of
the software to the VT DOC.
1.1.4 Contractor is responsible for providing complete telephone services at all Vennont Correctional Facilities. Inmate
telephone services include: collect calling, pre-paid collect calling and card less debit calling.
1.1.5 The State reserves the right to approve all system administration personnel who have access to the system and to
conduct background investigations of all assigned system administration contractor employees.
1.1.6 Call charges and rates are as noted below - the listed rates are exclusionary of local, state and federal taxes:
- 3-
�Collect Callin2 Information
Collect Call Rates
~
"
1<
Call Type
Operator Charge
Per
Minute
''iiu"
Local Call
$1.25
$0.07
1:>
IntraState (In-state Long Distance)
$1.25
$0.15
-0
InterState (Out-of-state Long Distance)
$1.25
$0.15
International
N/A
N/A
~
U
Pre-Paid Collect Callin2 Information
Collect Call Rates
1:>
~
Call Type
o "
U1<
Local Call
Operator Charge
til
-0'"
"",U'"
.~=
"
~
""
Per
Minute
$1.00
$0.06
IntraState (In-state Long Distance)
$1.00
$0.10
InterState (Out-of-state Long Distance)
$1.00
$0.10
International
$3.00
$0.50
Debit Callin2 Information
Debit Call Rates
Per
~
"
Cal! Type
'ii
Local Call
$0.25
$0.05
];
IntraState (In-state Long Distance)
$0.50
$0.10
"
InterState (Out-of-state Long Distance)
$0.50
$0.10
International
$1.00
$0.50
~
U
(:)
Operator Charge
Minute
1.2
Contractor Responsibilities - Equipment and Software
1.2.1 Contractor shall provide a complete turnkey solution including all equipment, software, and infrastructure
necessary for the ITS. These services include but are not limited to telephone sets, wiring, connectors, jacks,
security and monitoring systems.
1.2.2 Contractor is responsible for all equipment, software, and infrastructure including Contractor network and Internet
connectivity in the ITS in its entirety or its individual component'; including, but not limited to normal wear/use,
inmate abuse, natural disaster or inmate Unrest. System and/or component replacement(s) will be performed at no
cost to the State and will occur immediately upon notification to the Contractor ofthe system problem by the
Facility or State designee.
1.2.3 Contractor shall provide Basic Cellular Detection hardware and Contractor's Cellular Data Management
application at no cost to the State.
1.3
Contractor Responsibilities -Initial and Ongoing Installations and Deployment
1.3.1 Contractor shall upgrade all State facilities from the current Inmate Call Manager (ICM) solution to the ICM V
platform in accordance with the Project Plan and Tirneline included as Attachment H.
1.3.2 The State shall be responsible only for making the space for the telephones available to the Contractor. The State
shall not be obliged to make any improvements to the space provided for the telephones and the Contractor
'
equipment.
~
-4-
..
I
�1.3.3 Contractor shall submit plans for any updates and/or upgrades to the State project manager for prior written
approval which approval shall not be unreasonably withheld or delayed.
1.3.4 Contractor agrees to install and maintain the quantity ofteiephones required by the State as provided for in this
contract. All telephone/computer wiring that could affect State infrastructure must be approved by the State of
Vermont Department of Innovation and Information in advance.
1.3.5 Contractor shall install any additional telephones, and monitoring and recording equipment at no cost to the State
as reasonably requested. This includes expansion of any existing facility or newly constructed facility throughout
the state. Any new facilities will be added to the contract through an amendment and will be afforded the same
terms and conditions.
1.3.6 Contractor shall provide and install adequate surge and lightning protection equipment on all lines used for the
ITS. Uninterruptable Power Supply (UPS) units must be adequate for the size of each facility and robust enough to
sustain system functionality for a minimum of30 minutes in the event ofa power outage. Adequacy must be
documented based on UPS manufacturer's recommendations. The Contractor must provide, install and maintain
(accordfng to manufacturer's specifications) all ITS UPS equipment at each of the facilities. The Contractor must'
replace all UPS equipment upon expiration of the manufacturer's life cycle of the installed- product. The use of
traditional "power strips" for surge protection is not acceptable.
1.3.7 Contractor is responsible for clean up and removal of all debris and packaging material resulting from work
performed at no cost to the State.
1.3.8 Contractor shall restore to original condition, at no cost to the State, any State property damaged during
maintenance, installation or removal by personnel associated with the Contractor, including repairs to walls,
ceilings. etc.
] .3.9 Contractor shall provide the State with a list oftelephone numbers, serial numbers, and locations of each unit.
1.4 Station Equipment Specifications
104.1 Contractor shall subscribe to the Line Information Data Base (LlDB) for validation purposes. The Contractor shall
query this database for each inmate call and process only those calls which do not have Billed Number Screening
(BNS) or Billed to Numbers (BTN). The Contractor must assume all responsibility for the cost ofthe validation°.
1.4.2 Contractor shall provide sturdy, non-coin, vandal resistant and steel armored composed of durable, tamper-free
equipment suitable for a detention environment. The equipment must contain no removable parts.
].4.3 Contractor shall provide a sufficient number of telephone lines to the ITS to prevent inmates from receiving busy
signals more than 0.5% ofthe time. Contractor will provide monthly reports to the State contract manager proving
compliance in this area.
1.4.4 Contractor shall provide accommodations necessary to comply with Americans with Disabilities Act (ADA)
requirements, including but not Hmited to providing telephones which are accessible to persons in wheelchairs,
persons that are deaf, persons with physical impediments and persons who are blind. Systems provided must be
compatible with Telephone Devices for the Deaf (TDD), voice activated andlor Brai!.
104.5 During the call set up process, the ITS shall provide a pre-recorded announcement identifYing the call is coming
from a specific inmate and from a Correctional Facility. Called parties, when receiving a conect or pre-paid collect
call, shall have the option to receive a rate quote .during the call set-up process.
1.4.6 The ITS shall process calls on a selective linguistic basis: English and Spanish. Contractor will provide additional
languages at the request of the State within 30 days at no cost to the State.
1.4.7 The ITS shall provide a recording back to the inmate detailing why a call was not completed.
1.4.S Contractor shall ensure called parties with rotary phones must positively accept any call placed via the ITS. The
State does not wish to utilize passive acceptance in any case.
tf\)n
-5-
I
tJ
�1.5
Reporting Requirements
1.5.1 Contractor shall provide reporting and querying methods and capabilities to designated State personnel which
provide maximum flexibility, interface with commissary/inmate accounting system provider and speed.
1.5.2 Contractor shall work with State project manager to ensure all necessary reporting capabilities are in place for both
security and financiaVadministrative staff. Contractor shall assist designated State personnel in customizing
reports and query methods as requested.
1.5.3 Contractor shall supply monthly revenue reports by individual facility and call type.
1.6
Data Storage
1.6.1 Contractor shall maintain off-site storage of call detail records in a minimum of three (3) locations to avoid any
possibility of call detail records being" lost. Call Detail Records are created and stored in the primary data center
and immediately replicated to the secondary and tertiary back-up data centers.
.
1.6.2 Contractor shall store all call detail records, including attempted and completed calls for the full term of the
contract plus three (3) years.
1.6.3 Contractor shall provide access to designated State personnel to access call detail records from workstation(s) or
remote computers. The workstation(s) shall provide the capability to copy the Call Detail Records ontoa Compact
Disc (CD)/DVD.
1.7 Security Features
1.7.1 Contractor shall ensure the integrity ofthe ICM system at all times, allowing only designated State personnel
access to the system based on assigned security levels detennined by the State.
1.7.2 Contractor shall provide an "informant" line. Calls to the "informant" line shall be free and shall be routed via the
ITS to a destination designated by the State. Ifso requested by the State, the destination for the "informant" line
may be an automated voicemail box.
1.7.3 The ITS shall display Contractor's toll-free customer service line on the called party's calling number
identification (caller ID) system.
1.7.4 The ITS shan prohibit direct-dialed calls of any type, access to "411" information service, access to ''911'', access
to any toll-free andlor pay per service lines as well as access to multiple long distance carriers via 950, 800, 10 10XXX numbers, etc.
1.7.5 The ITS shall prevent inmates from circumventing the telephone systems, i.e. using the "con" line.
1.7.6 The ITS must be able to be shutdown quickly and selectively. The State must be able to shutdown the ITS by cutoff switches at several locations including, but not limited to:
• At demarcation location - total Facility telephones
• By central control center - select telephones
• By select housing units - control center
1.7.7 Contractor ensures no inmate telephone shall be capable of receiving an incoming call.
1.7.8 The ITS, upon detection of a three way call (call forwarding and conference calls, etc.), shall have the capability to
terminate the call immediately. The ITS will playa message, approved by the State, to the inmate or called party
prior to tenninating the call.
1.7.9 The ITS will prevent both the inmate and the called party from speaking/hearing one another until positive
acceptance has been completed. Only once positive acceptance has been completed may billing begin.
ai'
1.7.10 The ITS shall be capable of limiting the length of a call, providing the dial tone at certain times ofthe day and
.
allowing a maximum number of minutes per inmate, per month.
-6-
i
!
�1.7.11 Contractor will provide the State with Reverse Lookup as well as Keyword Search at no cost to the State.
1.8 Personal Identification Number (PIN) Application - pes does not yet have voice recognition/voice print
1.8.1 Contractor will implement a system of Personal Identification Numbers (PIN) for each inmate to use in making
telephone calls and utilizing the ITS. Upon assigning PIN to an inmate. contractor shall have a written agreement,
requiring the inmate to sign, notifYing himlher that all telephone calls via the ITS will be recorded and monitored.
1.8.2 Upon initialization of the first outgoing telephone call by each inmate, the ITS shall make sample voiceprints of
their name. The ITS shall make a recording ofthe voiceprint that will later be used to initiate all future calls by the
inmate.
1.8.2 Contractor shall provide the State with the llbility to use the voice recognition technology to obtain forensic
intelligence as part of internal and criminal investigatory matters no later than October 1.2011.
1.8.3 The ITS shall be capable of restricting use of the ITS by individual PIN, by unit, by facility, and blocking outgoing
calls to specified telephone numbers.
Fraud Management
1.9.1 The ITS shall detect the difference between an accepted call, answering machine, busy signal or other telephone
activity and only allow positive accepted calls to be processed. All other types shall result in the inmate hearing a
voice prompt explaining why the call was not completed.
1.9
1.9.2 The ITS shall allow call blocking of specific numbers by inmate PIN, telephones or group of telephones.
1.9.3 The ITS shall have the capability to assign pre-approved calling numbers (PAN) according to inmate PIN.
1.9.4 The ITS shall provide the called party. the ability to block all future calls from a State facility.
1.10 Call Monitoring & Recording
1.10.1 Contractor shall store all call recordings and ensure instant availability online (via ICM) for a minimum of 45 days.
1.l0.2 The ITS shall be able to simultaneously listen to and record inmate telephone conversations.
1.10.3 Contractor shall provide signage on each inmate telephone stating calls will be monitored and recorded.
1.11 Training
1.11.1 Contractor shall provide training to State staff at each location sufficient to enable successful use of the ITSIlCM.
Additional training shall be provided as requested throughout the life ofthis contract at no cost to the State.
1.l1.2 Contractor shall provide training documentation, both hard copy (2 manuals for each facility and Central Office)
and electronically, to the State at no cost to the State. All manuals shall become property of the State.
1.11.3 Contractor shall provide infonnational pamphlets for inmates' relatives to the applicable features and
functionalities of the ITS, when requested by the State and at no cost to the State.
- 7-
�1.12 General Maintenance
1.12.1 Contractor shall provide the necessary labor, parts, materials, and transportation to maintain all inmate telephones
in good working order and in compliance with the equipment manufacturer's specifications at no cost to the State.
1.12.2 The ITS shall provide for continuous on-line diagnostics and supervision, as well as local remote offline system
control access for advanced programming and diagnostics. Access to the built-in advanced diagnostics and
program control shall be accessible vIa modem by service center personnel and shall provide failure reports,
service history and other diagnostics.
1.123 Contractor shaH provide the State with customer service, including repairs and maintenance, as outlined in the
Service Level Agreement detailed in Attachment G. Contractor shall provide monthly reports on the ticketing
system to the State contract manager.
1.12.4 Contractor shall provide the State with a complete list of business, cellular and pager numbers for its
contractors/subcontractors, managers, administrators, technicians etc.
1.12.5 Contractor shall provide the State with a full-time administrator to manage the ITS, train, support and assist facility
end-users with software system and telephone problems. Managing the ITS includes, but is not limited to,
activating accounts manually when automation fails; setting up call blocks; setting up PAN lists; assigning,
recording and maintaining inmate PIN numbers; responding to requests and complaints from both the community
and inmate population; arranging for repair of onsite equipment as necessary; monitoring calls to alert staff of a
security breach; and reporting three-way call attempts. In addition, the on-site administrator shall manage all
externallegal requests for copies of inmate telephone recordings and testify as to chain of custody.
1.12.6 Contractor shall conduct monthly "walk throughs" of all State facilities to physically inspect imnate telephones and
other Contractor equipment. These monthly visits must be scheduled one month in advance with State facility
security staff to provide ample time for security staff scheduling.
1.13 Transition Plan
1.13.1 Contractor agrees to remove its equipment at the conclusion of the contract in a manner that will allow the reuse of
that wire distribution to the extent practicable.
1.13.2 Contractor agrees the workstations and associated infrastructure shall become the property of the State at the
expiration, cancellation or tennination of this contract. All call records, documentation, reports, data, etc. that are
contained in the inmate telephone system are exclusive property of the State and shall be provided on demand in a
mutually agreed upon format at no cost to the State.
1.13.3 Contractor shall discontinue providing service or accepting new assignments under the tenns ofthe contract, on a
date specified by the State. Contractor agrees to continue providing all services in accordance with the terms and
conditions, requirements and specifications of the contract for a period not to exceed ninety (90) calendar days
after the expiration, tennination or cancellation date on the same tenns and conditions set forth in this contract.
1.13.4 Commissions will be due and payable by the Contractor to the State at the compensation rate provided in the
contract until collect, debit andlor pre-paid calls are no longer handled by the Contractor. (Not to exceed ninety
(90). days.)
-8-
�2. SCOPE OF WORK INMATE ACCOUNTING SYSTEM AND COMMISSARY SERVICES
2.1
General Objectives
2.1.1 Contractor shall provide State with an automated inmate accounting solution that meets all business requirements
and addresses the accounting needs, of the State. Contractor shall support their own software. Technical support
must be provided 2417/365 by Contractor.
2.1.2 Contractor shall provide, support and maintain any software, hardware, interfaces, and communications
infrastructure required to operate the inmate account solution. Contractor shall provide their own Internet
connectivity, e-mail, and account management.
2.1.3 Contractor shall deliver high quality commissary services to the inmates ofthe State. Contractor shall provide
weekly delivery to each of the State facilities per an agreed upon schedule.
2.1.4 Contractor shall maintain a market price philosophy with regard to the retail selling price of the commissary items
(no price shall be higher than what a local convenience store charges for the same/similar item). Contractor shall
maintain per unit costs for commissary items previously available to State inmates for a minimum of one year. All
price changes must be pre-approved by the State.
2.1.5 Contractor recognizes simultaneous use by multiple users throughout the State is a necessity. The solution shall
have the ability to designate security/access/utilization levels to individual end-users.
2.2
Specific Requirements
2.2.1 Contractor shall provide an automated inmate accounting solution capable of being audited by the State or other
State authorized auditing facilities. The solution must be approved by the VT DOC and Agency of Human
Services. Contractor shall own, support and maintain, with its own employees, all aspects of the solution,
including all contractor supplied hardware, software, firmware, and communications/networking infrastructure.
Contractor shall provide the State with a royaJty free license to use the solution in the provision of commissary
services.
2.2.2 The solution must support a general ledger function, aJlow for a trial balance to be run at any time, contain the
ability to: set up annual fiscal maintenance and run ledger reports on any accounts or sub accounts contained
within the general ledger.
2.2.3 The solution shall interface with the State's jail management system (PASfTiny Term) at a frequency no less than
every 15 minutes. There shall be no cost to the State for said interface. Establishment of inmate accounts shall be
automated via the aforementioned interface. The solution shall allow for manual inmate account creation should
the need arise.
2.2.4 The solution shall contain an State required functionalities and reports. Contractor shall create required reports not
included in the standard installation within two weeks of receiving the State's specific request.
2.2.5 The solution shall provide for an accurate, cashless accounting of all inmate monies, expenses and purchases.
2.2.6 Contractor shall install the solution, provide ongoing support and maintenance and a toll free 24 hour emergency
line to minimize down time. Contractor shall have staff a minimum of six hours travel time to any State facility.
Contractor shall provide necessary solution hardware and will maintain same.
2.2.7 Contractor shall provide the State with all records pertaining to inmate accounts and commissary records at the
conclusion of this contract in electronic fonnat and media specified by the State.
2.2.8 Contractor shall provide a transition plan to convert existing and historical data housed in current system to data
within the new system.
2.2.9 Contractor shall provide, at no cost the State, a debit card release program allowing State staff to provide inmates
with a debit card bearing the balance of their commissary account versus cutting a physical check. Contractor shall
supply all necessary materials and components as well as fully support and maintain said program.
2.2.10 Contractor shall adhere to specified project timeline in accordance with Attachment I.
- 9-
�2.3 Inmate Commissary Service
2.3.1 Contractor and the State contract administrator shall mutually agree upon items to be sold through the commissary
program. No new items will be offered without the written permission of the State contract administrator.
Contractor will advise the State contract administrator of new products as they become available. Contractor shall
provide samples of products, upon request, to the State for review pursuant to security related concerns prior to
inclusion onto the commissary menu.
2.3.2 Contractor will provide State inmates with the ability to order commissary and debit telephone time via Telephone
Ordering. Contractor shall employ alternative ordering mechanisms should Telephone Ordering not be available
for reasons within the State's control:
2.3.3 All commissary orders will be combined, prepackaged, sorted by housing area and shipped within 24 hours of
agreed upon delivery schedule.
Food items shal1 be packaged and dated for individual consumption
All containers shall be made of non-breakable materials
No products shall contain alcohol
Inmates in general population shall be allowed to order commissary with a maximum purchase of $85/week
Inventory levels shall be maintained to ensure an order fill rate of at least 98%
Substitutions or backorders are not allowed
A method of restocking on returned orders must be available
All items sold must be jail appropriate
Commissary orders will be sent in clear, tamper proof, heat sealed plastic bags for the primary purpose of
security and accountability. A two part NCR receipt shall be sealed within the bag (inmate name, location, ID
number, items ordered, total of order and 2 signature lines)
Net sales will be defined as gross sales less sales of stamps, stamped envelopes, debit telephone time and sales
tax
All possible product containers shall be'''clear-view'', e.g. bottles, toothpaste, etc.
2.3.4 The State shall consult with Contractor regarding approved inmate items not listed on the commissary menu. The
State's desire is to have Contractor be the sole provider ofal1 inmate orders with heavy consideration given to
pricing. Should Contractor not readily stock/sell State approved items, i.e. extra-extra large clothing, specific
religious observance materials, shoe varieties, etc., Contractor shall make every effort to find such products and
add them to the commissary menu. Contractor and State shall mutually agree upon commissionable and noncommissionable status of added items .
.2.3.5 Contractor shall provide commissary menus, as requested, noting product number, product name, product size and
product cost. A master menu indicating, in addition to the above, whether or not the item is commissionable will
be provided to the State contract administrator.
2.3.6 Contractor shall adhere to specified project timeline in accordance with Attachment I.
2.4
Automated Self Service Options
2.4.1 Contractor shan provide a single website for the public to purchase commissary items and debit telephone time on
behalf of inmates, as well as deposit funds directly into an inmate's commissary account.
2.4.2 Contractor shall combine web product orders and inmate orders as not to exceed weekly inmate spending limits set
by the State.
2.4.3 Contractor shall supply designated State staifwith access to view web orders placed by family/friends for State
inmates.
2.4.4 Contractor shall provide a toll-free phone number for the public to deposit funds directly into an inmate's account.
2.4.5 Contractor shall install, configure and test lobby kiosks in three State facilities should the State request same. Said
kiosks will provide an on-site ability for visitors to deposit funds directly into any State inmate's commissary
account utilizing either cash or a credIt/debit card. ~:~~actor will fully support and maintain all components of ~
�the kiosks and their operations to include a daily ACH to the Inmate Trust Fund bank account. Contractor shall be
responsible for any and all costs associated with said kiosks and their activities.
2.4.6 Contractor shall assess the public utilizing the deposit functionalities noted in 2.4.1, 2.4.4 and 2.4.5 above, fees
based on the fee schedule directly below. The State shall approve any changes to said fee schedule prior to
implementation.
STANDARD FEE STRUCTURE
Kiosk
Kiosk
Web
Phone
Credit
Cash
$0.01 - $20.00
$2.95
$2.95
$3.00
$20.01 - $40.00
$40.01 - $60.00
$4.50
$5.50
$3.95
$5.50
$4.50
$5.50
$60.01 - $80.00
$6.25
$6.75
$3.00
$3.00
$3.00
Gross Amount Deposited
$80.01 - $90.00
$90.01 - $100.00
$100.01 - $120.00
$120.01 - $140.00
$140.01- $160.00
$161.00 - $180.00
$180.01- $200.00
$9.75
$10.25
$10.75
$11.25
$11.75
$12.25
$220.01 - $240.00
$12.75
$13.25
$240.01 - $260.00
$260.01- $280.00
$280.01- $300.00
$13.75
$14.25
$14.75
$200.01 - $220.00
$6.50
$7.25
$7.75
$10.75
$11.25
$11.75
$12.25
$12.75
$13.25
$13.75
$14.25
$14.75
$15.25
$15.75
$6.25
$6.75
$9.75
$10.25
$10.75
$11.25
$11.75
$12.25
$12.75
$13.25
$13.75
$14.25
$14.75
$3.00
$3.00
$3.00
$3.00
$3.00
$3.00
$3.00
$3.00
$3.00
$3.00
$3.00
$3.00
2.4.7 Contractor shall accommodate Post Office Box addresses for the public utilizing webservices, telephone services
andlor kiosk services to purchase items, debit telephone time andlor make deposits into inmates' accounts, at no
extra cost to the purchaser.
- II -
�ATTACHMENTB
CONTRACT FOR SERVICES
PAYMENT PROVISIONS
The State shall incur zero (0) costs in the implementation and execution of this contract throughout the length ofthe
contract. This contract is to provide State inmates with an inmate telephone, commissary and accounting system while
generating revenue (i.e. commissions) to sustain the State's Inmate Recreation Program/Fund while keeping costs to
inmates and their friends/families at a minimum.
All invoices outlined below will be paid directly from the Inmate Trust Fund bank account. At no time shall State funds
be encumbered or expended in relation to the services outlined in Attachment A.
1.
1.1
Contractor Payments
Commissary - Contractor shall invoice the State on a monthly basis. Invoices shall be itemized by week and
facility and shall outline stamp, stamped envelope and debit purchases for audit/reconciliation purposes as well as
co~mission calculations.
1.2
Telephone - Contractor shall invoice the State on a monthly basis for inmate debit telephone time. Invoices shall
reflect actual inmate debit time usage versus purchase. Invoices shall provide daily debit call detail to include
number of calls, minutes at a minimum.
2.
2.1
Commission
Contractor shall pay to the State a 37% commission on all'debit, collect and pre-paid collect inmate telephone
calls. Commissions will be remitted to the State no later than 45 days following month end.
2.2
Contractor shan pay to the State a 31 % commission on all commissary sales net of sales tax, exc1uding postage
stamps, stamped envelopes and debit telephone time purchases. Commissions will be remitted to the State no later
than 15 days following month end.
2.3
Contractor shall submit all commission payments to the State via ACH or wire transfer.
2.4
Contractor shall provide the State with back-up documentation supporting commission calculations for auditing
purposes.
2.5
Contractor agrees to a bi-annual commission/price point review with an eye toward reducing service/product
rates/prices as well as commission rates.
3.
3.1
Performance Measures
Refer to Attachment A - Section 1. Inmate Telephone Services, Subsection 3. Contractor Responsibilities, 1.3.1
"Contractor shall upgrade all State facilities from the current Inmate Call Manager (ICM) solution to the ICM V
platfonn in accordance with the Project Plan and Timeline included as Attachment H. "
Should Contractor fail to meet documented timelines a $500 per day fme shall be payable to the State unless
written approval for an extension is received by the State contract manager.
3.2
Statewide telephone downtime greater than .5% per month may result in a disincentive equal to $100 per total
hours of downtime payable to the State. Should there be zero (0) downtime statewide for a complete quarter (Jan Mar, Apr - Jun, Jul- Sept, Oct - Dec), Contractor may reduce one commission payment to the State by $100.
3.3
Refer to Attachment A - Section 1. Inmate Telephone Services, Subsection 12. General Maintenance, 1.12.3"Contractor shall provide the State with customer service, including repairs and maintenance, as outlined in the
Service Level Agreement detailed in Attachment G. Contractor shall provide monthly reports on the ticketing
system to the State contract manager."
Any instance, within Contractor's control, of non-compliance with the specifications in Attachment G may result
in monetary disincentives of$100 per instance payable to the State.
- 12-
�3.4
Should the escalation plan as provided by the Contractor, Attachment G, not be followed explicitly, other than for
reasons beyond Contractor's control, Contractor shall be liable for lost commissions during times that phones were
in need of repair or not properly operating. Lost commission will be calculated by multiplying the average number
of calls for each call type x (times) the then prevailing calling rates x (times) the commission rate. The specific
commission shall be calculated by the State and the State will advise the Contractor of all commissions due.
Contractor shall pay the calculated lost commission with the next commission payment due the State. Contractor
will be allotted time between the notification and the next commission payment to validate the lost commission.
3.5
Refer to Attachment A - Section 1. Inmate Telephone Services, Subsection 12. General Maintenance, 1.12.6"Contractor shall conduct monthly "walk throughs" of all State facilities to physically inspect inmate telephones
and other Contractor equipment. These monthly visits must be scheduled one month in advance with State facility
security staff to provide ample time for security staff scheduling."
Any visit not attended, within Contractor's control, when scheduled shall result in Contractor being billed for costs
associated with scheduling additional security staff necessary for the "walk through". (These funds will be
deposited into the State's general fund as a refund of expenditure.)
3.6
Commissary orders are to be delivered per the agreed upon schedule between Contractor and the State. Any
instances, within Contractor's control, (including subcontractors}, oflate or missed deliveries shall result in a $500
payment due to the State for each day delivery is late. Any quarter, (Jan - Mar, Apr - Jun, Jul- Sept, Oct - Dec),
with zero (O) late or missed deliveries shall result in a one time $500 reduction in the commissary commissions
payable to the State.
3.7
Commissary orders are to be delivered in boxes durable enough to support contents. Boxes received by the State
in unacceptable (i.e. crushed, broken, leaking, etc.) conditions may result in a $100 per box payment due to the
State. This payment is in addition to any credits given 'for damaged products. Any quarter, (Jan - Mar, Apr - Jun,
Jul ~ Sept, Oct -Dec), in which zero (O) boxes are received in unacceptable condition may result in a-one time
$500 reduction in the commissary commissions payable to the State.
3.8
Refer to Attachment A - Section 2. Inmate Accounting System and Commissary Services, subsection 2.2.10"Contractor shall adhere to specified project timeline in accordance with Attachment I.".
Should Conttactor fuil to meet documented timelines a $500 per day fine shall be payable to the State unless
written approval for an extension is received by the State contract manager.
3.9
Refer to Attachment A - Section 2. Inmate Accounting System and Commissary Services, subsection 2.3.3"Inventory levels shall be maintained to ensure an order fill rate of at least 98%".
Average weekly fill rates less than 98% may result in a disincentive of $100 per .1 % point of shortfall, payable to
the State. Average weekly fill rates greater than 98.5% may result in a once per month commissary commission
reduction of $300.
3.10 Refer to Attachment A - Section 2. Inmate Accounting System and Commissary Services, subsection 2.3.6"Contractor sh~l adhere to specified project timeline in accordance with Attachment I.".
Should Contractor fuil to meet documented timelines a $500 per day fine shall be payable to the State unless
written approval for an extension is received by the State contract manager.
3.11
Credits for missing or stale dated products (while under Contractor's control) in excess of an average weekly statewide rate of2% of quantity (not monetary value) may result in payment due the State equal to the total amount of
credits.
Contractor shall submit all invoices to:
Inmate Telephone/Commissary/Accounting Contract Manager
VT Department of Corrections, Central Business Office
103 S. Main St.
Waterbury, VT 05671-1001
- 13 -
�ATTACHMENTC
CUSTOMARY PROVISIONS FOR CONTRACTS AND GRANTS
1.
Entire Agreement. This Agreement, whether in the form of a Contract, State Funded Grant, or Federally Funded
Grant, represents the entire agreement between the parties on the subject matter. All prior agreements,
representations, statements, negotiation~, and understandings shall have no effect.
2.
Applicable Law. This Agreement will be governed by the laws of the State of Vermont
3.
Definitions: For purposes ofthis Attachment, "Party" shall mean the Contractor, Grantee or Subrecipient, with
whom the State of Vermont is executing this Agreement and consistent with the form of the Agreement.
4.
Appropriations: If appropriations are insufficient to support this Agreement, the State may cancel on a date agreed
to. by the parties or upon the expiration or reduction of existing appropriation authority. In the case that this
Agreement is funded in whole or in part by federal or other non-State funds, and in the event those funds become
unavailable or reduced, the State may suspend or cancel this Agreement immediately, and the State shall have no
obligation to fund this Agreement from State revenues.
5.
No Employee Benefits For Party: The Party understands that the State will not provide any individual retirement
benefits, group life insurance, group health and dental insurance, vacation or sick leave, workers compensation or
other benefits or services available to State employees, nor will the state withhold any state or federal taxes except as
required under applicable tax laws, which shall be determined in advance of execution of the Agreement. The Party
understands that all tax returns required by the Internal Revenue Code and the State of Vermont, including but not
limited to income, withholding, sales and use, and rooms and meals, must be filed by the Party, and infonnation as to
Agreement income will be provided by the State of Vermont to the Internal Revenue Service and the Vermont
Department of Taxes.
6.
Independence, Liability: The Party will act in an independent capacity and not as officers or employees of the State.
The Party shall defend the State and its officers and employees against all claims or suits arising in whole or in part
from any act or omission of the Party or of any agent ofthe Party. The State shall notifY the Party in the event of any
such claim or suit, and the Party shall immediately retain counsel and otherwise provide a complete defense against
the entire claim or suit. The Party shall notify its insurance company and the State within 10 days of receiving any
claim for damages, notice of claims, pre-claims, or service of judgments or claims, for any act or omissions in the
perfonnance of this Agreement.
After a final judgment or settlement the Party may request recoupment of specific defense costs and may file suit in
Washington Superior Court requesting recoupment. The Party shall be entitled to recoup costs only upon a showing
that such costs were entirely unrelated to the defense of any claim arising from an act or omission of the Party.
The Party shall indemnifY the State and its officers and employees in the event that the State, its officers or
employees become legally obligated to pay any damages or losses arising from any act or omission of the Party.
7.
Insurance: Before commencing work on this Agreement the Party must provide certificates of insurance to show that
the following minimum coverage is in effect. It is the responsibility ofthc Party to maintain current certificates of
insurance on file with the state through the tenn of the Agreement. No warranty is made that the coverage and limits
listed herein are adequate to cover and protect the interests of the Party for the Party's operations. These are solely
minimums that have been established to protect the interests of the State.
.
Workers Compensation: With respect to all operations perfonned, the Party shall carry workers' compensation
insurance in accordance with the laws of the State ofVennont.
General Liability and Propertv Damage: With respect to all operations perfonned under the Agreement, the
Party shall carry general liability insurance having all major divisions of coverage including, but not limited to:
Premises - Operations
Products and Completed Operations
Personal Injury Liability
- 14-
�Contractual Liability
The policy shall be on an occurrence form and limits shall not be less than:
$1,000,000 Per Occurrence
$1,000,000 General Aggregate
$1,000,000 Products!Completed Operations Aggregate
$ 50,000 Fire! Lega1!Liability
Party shall name ilie State ofVerrnont and its officers and employees as additional insureds for liability arising out of
this Agreement.
Automotive Liability: The Party shall carty automotive liability insurance covering all motor vehicles, including
hired and non-owned coverage, used in connection with the Agreement. Limits of coverage shall not be less
than: $1,000,000 combined single limit,
Party shall name the State of Vermont and its officers and employees al) additional insureds for liability arising out of
this Agreement.
Professional Liability: Before commencing work on this Agreement and throughout the term of this
Agreement, the Party -shall procure and maintain professional liability insurance for any and all services
performed under this Agreement, with minimum coverage of $NIA per occurrence, and $NIA aggregate.
8.
Reliance by the State on Representations: All payments by the State under this Agreement will be made in reliance
upon the accuracy of all prior representations by the Party, including but not limited to bills, invoices, progress
reports and other proofs of work.
9.
Requirement to Have a Single Audit: In the case that this Agreement is a Grant that is funded in whole or in part by
federal funds, and ifiliis Subrecipient expends $500,000 or more in federal assistance during its fiscal year, the
Subrecipient is required to have a single audit conducted in accordance with the Single Audit Act, except when it elects
to have a program specific audit.
The Subrecipient may elect to have a program specific audit if it expends funds under only one federal program and
the federal program's laws, regulating or grant agreements do not require a financial statement audit of the Party.
A Subrecipient is exempt if the Party expends less than $500,000 in total federal assistance in one year.
The Subrecipient will complete the Certification of Audit Requirement annually within 45 days after its fiscal year
end. If a single audit is required, ilie sub-recipient will submit a copy of the audit report to ilie primary pass-through
Party and any oilier pass-ilirough Party that requests it wiiliin 9 monilis. If a single audit is not required, the
Subrecipient will submit ilie Schedule of Federal Expenditures within 45 days. These forms wiIl be mailed to ilie
Subrecipient by the Department of Finance and Management near the end of its fiscal year. These forms are also
available on the Finance & Management Web page at: http://finance.vermont.gov/forms
10. Records Available for Audit: The Party will maintain all books, documents, payroll papers, accounting records and
other evidence pertaining to costs incurred under this agreement and make them available at reasonable times during
the period ofthe Agreement and for three years thereafter for inspection by any authorized representatives of the
State or Federal Government. If any litigation, claim, or audit is started before the expiration of the three year period,
the records shall be retained until all litigation, claims or audit findings involving the records have been resolved. The
State, by any authorized representative, shall have the right at all reasonable times to inspect or otherwise evaluate
the work performed or being performed under this Agreement.
11. Fair Employment Practices and Americans with Disabilities Act: party agrees to comply with the requirement of
Title 2IV.S.A. Chapter 5, Subchapter 6, relating to fair employment practices, to ilie full extent applicable. Party
shall also ensure, to the full extent requIred by the Americans wiili Disabilities Act of 1990 iliat qualified individuals
with disabilities receive equitable access to the- services, programs, and activities provided by the Party under this
Agreement. Party further agrees to include this provision in all subcontracts.
- 15 -
�12. Set 00': The State may set off any sums which the Party owes the State against any sums due the Party under this
Agreement; provided, however, that any set off of amounts due the State of Vermont as taxes shall be in accordance
with the procedures more specifically provided hereinafter.
13. Taxes Due to the State:
a.
Party understands and acknowledges responsibility, if applicable, for compliance with State tax laws,
including income tax withholding for employees performing services within the State, payment of use tax on
property used within the State, corporate andlor personal income tax on income earned within the State.
b.
Party certifies under the pains and penalties of perjury that, as ()fthe date the Agreement is signed, the Party
is in good standing with respect to, or in full compliance with, a plan to pay any and all taxes due the State
ofVennont.
c,
Party understands that final payment under this Agreement may be withheld if the Commissioner of Taxes
determines that the Party is not in good standing with respect to or in full compliance with a plan to pay any
and all taxes due to the State of Vermont.
Party also understands the State may set off taxes (and related penalties, interest and fees) due to the State of
Vermont, but only if the Party has failed to make an appeal within the time allowed by law, or an appeal has been
taken and finally determined and the Party has no further legal recourse to conte~t the amounts due.
14. Child Support: (Applicable if the Party. is a natural person, not a corporation or partnership.) Party states that, as of
the date the Agreement is signed, he/she:
a.
is not under any obligation to pay child support; or
b.
is under such an obligation and is in good standing with respect to that obligation; or
c.
has agreed to a payment plan with the Vermont Office of Child Support Services and is in full compliance
with that plan.
Party makes this statement with regard to support owed to any and all children residing in Vermont. In addition, if
the Party is a resident of Vermont, Party makes this statement with regard to support owed to any and all children
residing in any other state or territory .ofthe United States.
15.
Sub~Agreements: Party shall not assign, subcontract or subgrant the performance of his Agreement or any portion
thereofto any other Party without the prior written approval ofthe State. Party also agrees to include in subcontract
or subgrant agreements a tax certification in accordance with paragraph 13 above.
Notwithstanding the foregoing, the State agrees that the Party may assign this agreement, including all of the Party's
rights and obligations hereunder, to any successor in interest to the Party arising out of the sale of or reorganization
ofthe Party.
16. No Gifts or Gratuities: Party shall not give title or possession of any thing of substantial value (including property,
currency, travel and/or education programs) to any officer or employee of the State during the tenn of this
Agreement.
17, Copies: All written reports prepared under this Agreement will be printed using both sides of the paper.
18, Certification Regarding Debarment: Party certifies under pains and penalties of perjury that, as of the date thatthis
Agreement is signed, neither Party nor Party's principals (officers, directors, owners, or partners) are presently
debarred, suspended, proposed for debarment, declared ineligible or excluded from participation in federal programs
or programs supported in whole or in part by federal funds.
State of Vermont - Artachment C
Revised AHS - 4-06-09
- 16-
�ATTACHMENT E
BUSINESS ASSOCIATE AGREEMENT
THIS BUSINESS ASSOCIATE AGREEMENT ("AGREEMENT") IS ENTERED INTO BY AND BETWEEN
THE STATE OF VERMONT AGENCY OF HUMAN SERVICES OPERATING BY AND THROUGH ITS
DEPARTMENT, OFFICE, OR DIVISION OF DEPARTMENT OF CORRECTIONS ("COVERED ENTITY") AND
PUBLIC COMMUNICATIONS SERVICES, INC. ("BUSINESS ASSOCIATE") AS OF 10/0112010
("EFFECTIVE DATE"). THIS AGREEMENT SUPPLEMENTS AND IS MADE A PART OF THE CONTRACT
TO WHICH IT IS AN ATTACHMENT.
Covered Entity and Business Associate enter into this Agreement to comply with standards promulgated under the Health
Insurance Portability and Accountability Act of 1996 ("HIPAA") including the Standards for the Privacy ofIndividuaJJy
Identifiable Health Information at 45 CFR Parts 160 and 164 ("Privacy Rule") and the Security Standards at 45 CFR Parts
160 and 164 ("Security Rule"), as amended by subtitle D of the Health Information Technology for Economic and
Clinical Health Act.
The parties agree as follows:
1.
Definitions. All capitalized tenns in this Agreement have the meanings identified in this Agreement, 45 CFR Part
160, or 45 CFR Part 164.
The term "Services" includes all work performed by the Business Associate for or on behalf of Covered Entity that
requires the use and/or disclosure of protected health information to perform a business associate function described
in 45 CFR 160.103 under the definition of Business Associate.
The term "Individual" includes a person who qualifies as a personal representative in accordance with 45 CFR
164.502(g).
The term "Breach" means the acquisition, access, use or disclosure of protected health information (PHI) in a
manner not permitted under the HIP AA Privacy Rule, 45 CFR part 164, subpart E, which compromises the security
or privacy of the PHI. "Compromises the security or privacy ofthe PHI" means poses a significant risk of financial,
reputational or other harm to the individua1.
2.
Permitted and Required Uses/Disclosures of PHI.
2.1 Except as limited in this Agreement, Business Associate may use or disclose PHI to perform Services, as
specified in the underlying contract with Covered Entity. Business Associate shall not use or disclose PHI in
any manner that would constitute a violation of the Privacy Rule if used or disclosed by Covered Entity in
that manner. BUSiness Associate may not use or disclose PH] other than as permitted or required by this
Agreement or as Required by Law.
2.2
3.
Business Associate may make PHI available to its employees who need access to perform Services provided
that Business Associate makes such employees aware of the use and disclosure restrictions in this Agreement
and binds them to comply with such restrictions. Business Associate may only disclose PHI for the purposes
authorized by this Agreement: (a) to its agents (including subcontractors) in accordance with Sections 8 and
16 or (b) as otherwise permitted by Section 3.
Business Activities. Business Associate may use PHI received in its capacity as a "Business Associate" to Covered
Entity if necessary for Business Associate's proper management and administration or to carty out its legal
responsibilities. Business Associate may disclose PHI received in its capacity as "Business Associate" to Covered
Entity for Business Associate's proper management and administration or to carry out its legal responsibilities if a
disclosure is Required by Law or if (a) Business Associate obtains reasonable written assurances via a written
agreement from the person to whom the information is to be disclosed that the PHI shall remain confidential and be
used or further disclosed only as Required by Law or for the purpose for which it was disclosed to the person and
(b) the person notifies Business Associate, within three business days (who in turn will notifY Covered Entity within
three business days after receiving notice of a Breach as specified in Section 5.1), in writing of any Breach of
Unsecured PHI of which it is aware. Uses and disclosures of PHI for the purposes identified in this Section must b e y ..
of the minimum amount of PHI necessary to accomplish such purposes.
- 17 -
�4.
Safeguards. Business Associate shall implement and use appropriate safeguards to prevent the use or disclosure of
PHI other than as provided for by this Agreement. With respect to any PHI that is maintained in or transmitted by
electronic media, Business Associate shall comply with 45 CFR sections 164.308 (administrative safeguards),
164.310 (physical safeguards), 164,312 (technical safeguards) and 164.316 (policies and procedures and
documentation requirements). Business Associate shall identifY in writing upon request from Covered Entity all of
the safeguards that it uses to prevent impennissible uses or disclosures of PHI.
5.
Documenting and Reporting Breaches.
5.1 Business Associate shall report to Covered Entity any Breach of Unsecured PHI as soon as it (or any of its
employees or agents) become aware of any such Breach, and in no case later than three (3) business days after
it (or any of its employees or agents) becomes aware of the Breach, except when a law enforcement official
detennines that a notification would impede a criminal investigation or cause damage to national security.
5.2 Business Associate shall provide Covered Entity with the names of the individuals whose Unsecured PHI has
been, or is reasonably believed to have been, the subject of the Breach and any other available infonnation that
is required to be given to the affected individuals, as set forth in 45 CFR §164.404(c), and, if requested by
Covered Entity, information necessary for Covered'Entity to investigate the impermissible use or disclosure.
Business Associate shall continue to provide to Covered Entity information concerning the Breach as it
becomes available to it.
5.3
When Business Associate detennines that an impennissible acquisition, use or disclosure of PHI by a member
of its workforce does not pose a significant risk of harm to the affected individuals, it shall document its
assessment of risk. Such assessment shall include: 1) the name of the person(s) making the assessment, 2) a
brief summary of the facts, and 3) a brief statement of the reasons supporting the determination oflow risk of
harm. When requested by Covered Entity, Business Associate shall make its risk assessments available to
Covered Entity.
6.
Mitigation and Corrective Action. Business Associate shall mitigate, to the extent practicable, any hannful effect
that is known to it of an impermissible use or disclosure of PHI, even if the impermissible use or disclosure does not
constitute a Breach. Business Associate shall draft and carry out a plan of corrective action to address any incident of
impermissible use or disclosure of PHI. If requested by Covered Entity, Business Associate shall make its mitigation
and corrective action plans available to Covered Entity.
7.
Providing Notice of Breaches.
7.1 If Covered Entity detennines that an- impermissible acquisition, access, use or disclosure of PHI for which one
of Business Associate's employees or agents was responsible constitutes a Breach as defined in 45 CPR
§164.402, and if requested by Covered Entity, Business Associate shall provide notice to the individuals
whose PHI was the subject of the Breach. When requested to provide notice, Business Associate shall consult
with Covered Entity about the timeliness, content and method of notice, and shall receive Covered Entity's
approval concerning these elements. The cost of notice and related remedies shall be borne by Business
Associate.
7.2 The notice to affected individuals shall be provided as soon as reasonably possible and in no case later than 60
calendar days after Business Associate reported the Breach to Covered Entity.
7.3
7.4
The notice to affected individuals shall be written in plain language and shall include, to the extent possible, 1)
a brief description of what happened, 2) a description of the types of Unsecured PHI that were involved in the
Breach, 3) any steps individuals can take to protect themselves from potential harm resulting from the Breach,
4) a brief description of what the Business associate is doing to investigate the Breach, to mitigate harm to
individuals and to protect against further Breaches, and 5) contact procedures for individuals to ask questions
or obtain additional information, as set forth in 45 CFR §164.404(c).
Business Associate shall notilY ·individuals of Breaches as specified in 45 CFR §164.404( d) (methods of
individual notice). In addition, when a Breach involves more than 500 residents of Vennont, Business
associate shall, if requested by Covered Entity, notify prominent media outlets serving Vennont, following the
_ 18 requirements set forth in 45 CFR § 164.406.
f
�8.
Agreements by Third Parties. Business Associate shall ensure that any agent (including a subcontractor) to whom
it -provides PHI received from Covered Entity or created or received by Business Associate on behalf of Covered
Entity agrees in a written agreement to the same restrictions and conditions that apply through this Agreement to
Business Associate with respect to such PHI. For example, the written contract must include those restrictions and
conditions set fQrth in Section 14. Business Associate must enter into the written agreement before any use or
disclosure of PHI by such agent. The written agreement must identifY Covered Entity as a direct and-intended third
party beneficiary with the right to enforce any hreach of the agreement concerning the use or disclosure of PHI.
Business Associate shaH provide a copy of the written agreement to Covered Entity upon request. Business
Associate may not make any disclosure of PHI to any agent without the prior written consent of Covered Entity.
9.
Access to PHI. Business Associate shall provide access to PHI in a Designated Record Set to Covered Entity or as
directed by Covered Entity to an Individual to meet the requirements under 45 CFR 164.524. Business Associate
shaU provide such access in the time and manner reasonably designated by Covered Entity. Within three (3)
business days, Business Associate shall forward to Covered Entity for handling any request for access to PHI that
Business Associate directly receives from an Individual.
10.
Amendment of PHI. Business Associate shaH make any amendments to PHI in a Designated Record Set that
Covered Entity directs or agrees to pursuant to 45 CFR 164.526, whether at the request of Covered Entity or an
Individual. Business Associate shall "make such amendments in the time and manner reasonably designated by
Covered Entity. Within three (3) business days, Business Associate shall forward to Covered Entity for handling
any request for amendment to PHI that Business Associate directly receives from an Individual.
11. Accounting of Disclosures. Business Associate shall document disclosures of PHI and all infonnation related to
such disclosures as would be required for Covered Entity to respond to a request by an Individual for an accounting
of disclosures of PHI in accordance with 45 CFR 164.528. Business Associate shaH provide such information to
Covered Entity or as directed by Covered Entity to an Individual, to permit Covered Entity to respond to an
accounting request. Business Associate shall proVide such information in the time and manner reasonably designated
by Covered Entity. Within three (3) business days, Business Associate shall forward to Covered Entity for handling
any accounting request that Business Associate directly receives from an lndividual.
12.
Books and Records. Subject to the attorney-client and other applicable legal privileges, Business Associate shall
make its internal practices, books, and records (including policies and procedures and PHI) relating to the use and
disclosure of PHI received from Covered Entity or created or received by Business Associate on behalf of Covered
Entity available to the Secretary in the time and manner designated by the SecretaI)'. Business Associate shall make
the sarne information available to Covered Entity (without regard to the attorney-client or other applicable legal
privileges) upon Covered Entity's request in the time and manner reasonably designated by Covered Entity so that
Covered Entity may determine whether Business Associate is in compliance with this Agreement.
13.
Termination.
14.
13.l
This Agreement commences on the Effective Date and shall remain in effect until terminated by Covered
Entity or until all of the PHI provided by Covered Entity to Business Associate or created or received by
Business Associate on behalf of Covered Entity is destroyed or returned to Covered Entity subject to Section
17.7.
13.2
If Business Associate breaches any material term ofthis Agreement, Covered Entity may either: (a) provide
an opportunity for Business Associate to cure the breach and Covered Entity may terminate this Contract
without liability or penalty if Business Associate does not cure the breach within the time specified by
Covered Entity; or (b) immediately terminate this Contract without liability or penalty if Covered Entity
believes that cure is not reasonably possible; or (c) if neither termination nor cure are feasible, Covered
Entity shall report the breach to the Secretary. Covered Entity has the right to seek to cure any breach by
business Associate and this right, regardless of whether Covered Entity cures such breach, does not lessen
any right or remedy available to Covered Entity at law, in equity, or under this Contract, nor does it lessen
Business Associate's responsibility for such breach or its duty to cure such breach.
ReturnlDestruction of PHI.
- 19-
�14.1
Business Associate in connection with the expiration or termination of this Contract shall return or destroy
all PHI received from Covered Entity or created or received by Business Associate on behalf of Covered
Entity pursuant to this Contract that Business Associate still maintains in any form or medium (including
electronic) within thirty (30) days after such expiration or termination. Business Associate shall not retain
any copies of the PHI. Business Associate shall certifY in writing for Covered Entity (1) when all PHI has
been returned or destroyed and (2) that Business Associate does not continue to maintain any PHI. Business
Associate is to provide this certification during this thirtY (30) day period.
14.2
Business Associate shall provide to Covered Entity notification of any conditions that Business Associate
believes make the return or des,truction of PHI infeasible. If Covered Entity agrees that return or destruction
is infeasible, Business Associate shall extend the protections of this Agreement to such PHI and limit further
uses and disclosures of such PHI to those purposes that make the return or destruction infeasible for so long
as Business Associate maintains such PHI.
15.
Penalties and- Training. Business Associate understands that: (a) there may be civil or criminal penalties for
misuse or misappropriation of PHI and (b) violations ofthis Agreement may result in notification by Covered Entity
to law enforcement officials and regulatory, accreditation, and licensure organizations. If requested by Covered
Entity, Business Associate shall participate in training regarding the use, confidentiality, and security of PHI.
16.
Security Rule Obligations. The follgwing provisions of this Section apply to the extent that Business Associate
creates, receives, maintains or transmits Electronic PHI on behalf of Covered Entity.
17.
16.1
Business Associate shall implement and use administrative, physical, and technical safeguards in
compliance with 45 CFR sections 164.308, 164.310, and 164.312 with respect to the Electronic PHI that it
creates, receives, maintains or transmits on behalf of Covered Entity. Business Associate shall identifY in
writing upon request from Covered Entity all of the safeguards that it uses to protect such Electronic PHI.
16.2
Business Associate shall ensure that any agent (including a subcontractor) to whom it provides Electronic
PHI agrees in a written agreement to implement and use administrative, physical, and technical safeguards
that reasonably and appropriately protect the Confidentiality, Integrity and Availability of the Electronic
PHI. Business Associate must enter into this written agreement before any use or disclosure of Electronic
PHI by such agent. The written agreement must identifY Covered Entity as a direct and intended third PartY
beneficiary with the right to enforce any breach of the agreement concerning the use or disclosure of
Electronic PHI. Business Associate shall provide a copy of the written agreement to Covered Entity upon
request. Business Associate may not make any disclosure of Electronic PHI to any agent without the prior
written consent of Covered Entity.
16.3
Business Associate shall report in writing to Covered Entity any Security Incident pertaining to such
Electronic PHI (whether involving Business Associate or an agent, including a subcontractor). Business
Associate shall provide this wrjtten report as soon as it becomes aware of any such Security Incident, and in
no case later than three (3) business days after it becomes aware of the incident. Business Associate shall
provide Covered Entity with the information necessary for Covered Entity to investigate any such Security
Incident.
16.4
Business Associate shall comply with any reasonable policies and procedures Covered Entity implements to
obtain compliance under the Security Rule.
MisceUaneous.
17.1 In the event of any conflict or inconsistency between the terms of this Agreement and the terms of the
Contract, the terms of this Agreement shall govern with respect to its subject matter. Otherwise the terms of
the Contract continue in effect.
17.2
Business Associate shall cooperate with Covered Entity to amend this Agreement from time to time as is
necessary for Covered Entity to comply with the Privacy Rule, the Security Rule, or any other standards
promulgated under HIPAA.
- 20-
�17.3
Any ambiguity in this Agreement shall be resolved to permit Covered Entity to comply with the Privacy
Rule, Security Rule, or any other standards promulgated under HIP AA.
17.4
In addition to applicable Vermont law, the parties shall rely on applicable federal law (e.g., HlPAA, the
Privacy Rule and Security Rule) in construing the meaning and effect of this Agreement.
17.5
As between Business Associate and Covered Entity, Covered Entity owns all PHI provided by Covered
Entity to Business Associate or created or received by Business Associate on behalf of Covered Entity.
17.6
Business Associate shall abide by the terms and conditions of this Agreement with respect to all PHI it
receives from Covered Entity or creates or receives on behalf of Covered Entity under this Contract even if
some of that infonnation relates to specific services for which Business Associate may not be a "Business
Associate" of Covered Entity under the Privacy Rule.
17.7
The provisions of this Agreement that by their terms encompass continuing rights or responsibilities shall
survive the expiration or tennination of this Agreement. For example: (a) the provisions of this Agreement
shall continue to apply if Covered Entity determines that it would be infeasible for Business Associate to
return or destroy PHI as provided in Section 14.2 and (b) the obligation of Business Associate to provide an
accounting of disclosures as set forth in Section II survives the expiration or termination of this Agreement
with respec~ to accounting requests, if any, made after such expiration or termination.
(AHS Rev: 112511 0)
- 21 -
�ATTACHMENTF
AGENCY OF HUMAN SERVICES' CUSTOMARY CONTRACT PROVISIONS
1. Agency of Human Services
Field Services Directors will share oversight with the department (or field office)
that is a party to the contract for provider performance using outcomes, processes, terms and conditions agreed to
under this contract.
2.
2-1-1 Data Base: The Contractor providing a health or hU!TIan services within Vermont, or near the border that is
readily accessible to residents of Vermont, will provide relevant descriptive information regarding its agency,
programs and/or contact and will adhere to the "InciusionlExclusion" policy of Vermont's 2-1-1. If included, the
Contractor will provide accurate and up to date information to their data base as needed. The "InciusionlExciusion"
policy can be found atwww.verrnont211.org"
3.
Medicaid Program Contractors:
Inspection of Records: Any contracts accessing payments for services through the Global Commitment to Health
Waiver and Vermont Medicaid program must fulfill state and federallega! requirements to enable the Agency of
Human Services (AHS), the United States Department of Health and Human Services (DHHS) and the Government
Accounting Office (GAO) to:
Evaluate through inspection or other means the quality, appropriateness, and timeliness of services performed;
and Inspect and audit any financial records of such Contractor or subcontractor.
Subcontracting for Medicaid Services: Having a subcontract does not terminate the Contractor, receiving funds under
Vermont's Medicaid program, from its responsibility to ensure that all activities under this agreement are carried out.
Subcontracts must specifY the activities and reporting responsibilities of the Contractor or subcontractor and provide
for revoking delegation or imposing other sanctions if the Contractor or subcontractor's perfonnance is inadequate.
The Contractor agrees to make available upon request to the Agency of Human Services; the Office of Vermont
Health Access; the Department of Disabilities, Aging and Independent Living; and the Center for Medicare and
Medicaid Services (CMS) all contracts and subcontracts between the Contractor and service providers.
Medicaid Notification ofTennination Requirements: Any Contractor accessing payments for services under the
Global Commitment to Health Waiver and Medicaid programs who terminates their practice will follow the Office of
Vermont Health Access, Managed Care-Organization enrollee notification requirements.
Encounter Data: Any Contractor accessing payments for setvices through the Global Commitment to Health Waiver
and Vennont Medicaid programs must provide encounter data to the Agency of Human Services and/or its
departments and ensure that it can be linked to enrollee eligibility files maintained by the State.
4.
Non-discrimination Based on National Origin as evidenced by Limited English Proficiency. The Contractor
agrees to comply with the non-discrimination requirements of Title VI of the Civil Rights Act of 1964,42 USC
Section 2000d, et seq., and with the federal guidelines promulgated pursuant to Executive Order 13166 of2000,
which require that contractors and subcontractors receiving federal funds must assure that persons with limited
English proficiency can meaningfully access services. To the extent the Contractor provides assistance to individuals
with limited English proficiency through the use of oral or written translation or interpretive services in compliance
with this requirement, such individuals cannot be required to pay for such services.
5.
Voter Registration. When designated by the Secretary of State, the Contractor agrees to become a voter registration
agency as defined by 17 V.S.A. §2103 (41), and to comply with the requirements of state and federal law pertaining
to such agencies.
- 22-
�6.
Drug Free Workplace Act. The Contractor will assure a drug-free workplace in accordance with 45 CFR Part 76.
7.
Privacy and Security Standards.
Protected Health Infonnation: The Contractor shall maintain the privacy and security of all individually identifiable
health information acquired by or provided to it as a part of the perfonnance of this contract. The Contractor shall
follow federal and state law relating to privacy and security of individually identifiable health infonnation as
applicable, including the Health Insurance Portability and Accountability Act (H1PAA) and its federal regnlations.
Substance Abuse Treatment Information: The confidentiality of any alcohol and drug abuse treatment infonnation
acquired by or provided to the Contractor or subcontractor shall be maintained in compliance with any applicable
state or federal laws or regulations and specifically set out in 42 CFR Part 2-.
Other Confidential Consumer Information: The Contractor agrees to comply with the requirements of AHS Rule No.
08-048 concerning access to information. The Contractor agrees to comply with any applicable Vennont State
Statute, including but not limited to 12 VSA §16l2 and any applicable Board of Health confidentiality regulations.
The Contractor shall ensure that all of its employees and subcontractors perfonning services under this agreement
understand the sensitive nature of the infonnation that they may have access to and sign an affinnation of
understanding regarding the infonnation's confidential and non-public nature.
Social Security numbers: The Contractor agrees to comply with all applicable Vermont State Statutes to assure
protection and security of personal infonnation, including protection from identity theft as outlined in Title 9,
Vennont Statutes Annotated, Ch. 62.
8.
Abuse Registry. The Contractor agrees not to employ any individual, use any volunteer, or otherwise provide
reimbursement to any individual in the performance of services connected with this agreement, who provides care,
custody, treatment, transportation, or supervision to children or vulnerable adults if there is_a substantiation of abuse or
neglect or exploitation against that individual. The Contractor will check the Adult Abuse Registry in the Departnlent of
Disabilities, Aging and Independent Living. Unless the Contractor holds a valid child care license or registration from
the Division of Child Development, Department for Children and Families, the Contractor shall also check the Central
Child Abuse Registry. (See 33 V.S.A. §49l9(a)(3) & 33 V.S.A. §6911 (c)(3».
9.
Reporting of Abuse. Neglect. or Exploitation. Consistent with provisions of 33 V.s.A. §4913(a) and §6903, any
agent or employee of a Contractor who, in the performance of services connected with this agreement, has contact
with clients or is a caregiver and who has reasonable cause to believe that a child or vulnerable adult has been abused
or neglected as defined in Chapter 49 or abused, neglected, or exploited as defined in Chapter 69 of Title 33 V.S.A.
shall make a report involving children to the Commissioner of the Department for Children and Families within 24
hours or a report involving vulnerable adults to, the Division of Licensing and Protection at the Department of
Disabilities, Aging, and Independent Living within 48 hours. This requirement applies except in those instances
where particular roles and functions are exempt from reporting under state and federal law. Reports involving
children shall contain the infonnation required by 33 V.S.A. §49l4. Reports involving vulnerable adults shall contain
the information required by 33 V.S.A. §6904. The Contractor will ensure that its agents or employees receive training
on the reporting of abuse or neglect to children and abuse, neglect or exploitation of vulnerable adults.
- 23-
�10. Intellectual' Property/Work Product Ownership. All data, technical infonnation, materials first gathered,
originated, developed, prepared, or obtained as a condition of this agreement and used in the performance of this
agreement - including, but not limited to all reports, surveys, plans, charts, literature, brochures, mailings, recordings
(video or audio), pictures, drawings, analyses, graphic representations, software computer programs and
accompanying documentation and printouts, notes and memoranda, written procedures and documents, which are
prepared for or obtained specifically for this agreement - or are a result of the services required under this grant shall be considered Itwork for hire" and remain the property of the State of Vermont, regardless of the state of
completion - unless otherwise specified in this agreement. Such items shall be delivered to the State of Vermont upon
30 days notice by the State. With respect to software computer programs and / or source codes first developed for the
State, all the work shal1 be considered "work for hire," i.e., the State, not the Contractor or subcontractor, shall have
full and complete ownership of all software computer programs, documentation and/or source codes developed.
The Contractor shan not sell or copyright a work product or item produced under this agreement without explicit
permission from the State.
If the Contractor is operating a system or application on behalfofthe State of Vermont, then the Contractor shall not
make information entered into the system or application available for uses by any other party than the State of
Vermont, without prior authorization by_ the State. Nothing herein shall entitle the State to pre-existing Contractor's
materials.
II. Security and Data Transfers. The State shall work with the Contractor to ensure compliance with all applicable
State and Agency of Human Services' policies and standards, especially those related to privacy and security. The
State will advise the Contractor of any new policies, procedures, or protocols developed during the term of this
agreement as they are issued and will work with the Contractor to implement any required.
The Contractor will ensure the physical and data security associated with computer equipment - including desktops,
notebooks, and other portable devices - used in connection with this agreement. The Contractor will also assure that
any media or mechanism used to store or transfer data to or from the State includes industry standard security
mechanisms such as continually up-ta-date mal ware protection and encryption. The Contractor will make every
reasonable effort to ensure media or data files transferred to the State are virus and spyware free. At the conclusion of
this agreement and after successful delivery of the data to the State, the Contractor shall securely delete data
(including archival backups) from the Contractor's equipment that contains individually identifiable records, in
accordance with standards adopted by the Agency of Human Services.
12. Computing and Communication: The Contractor shall select, in consultation with the Agency of Human Services'
Infonnation Technology unit, one of the approved methods for secure access to the State's systems and data, if
required. Approved methods are based"on the type of work performed by the Contractor as part of this agreement.
Options include, but are not limited to:
1.
Contractor's provision of certified computing equipment, peripherals and mobile devices, on a separate
Contractor's network with separate internet access. The Agency of Human Services' accounts mayor may not be
provided.
2.
State supplied and managed equipment and accounts to access state applications and data, including State issued
active directory accounts and application specific accounts, which follow the National Institutes of Standards and
Technology (NIST) security and the Health Insurance Portability & Accountability Act (HIPAA) standards.
The State will not supply e-mail accounts to the Contractor.
13. Lobbying. No federal funds under this agreement may be used to influence or attempt to influence an officer or
employee of any agency, a member of Congress, an officer or employee of Congress, or an employee of a member of
Congress in connection with the awarding of any federal contract, continuation, renewal, amendments other than
federal appropriated funds.
14. Non-discrimination. The Contractor will prohibit discrimination on the basis of age under the Age Discrimination
Act of 1975, on the basis of handicap under section 504 of the Rehabilitation Act of 1973, on the basis of sex under
Title IX of the Education Amendments,of 1972, or on the basis of race, color or national origin under Title VI Ofthe
-24·
.
.. .
r7l Iy
lfJ
�Civil Rights Act ofl964. No person shall on the grounds of sex (including, in the case of a woman, on the grounds
that the woman is pregnant) or on the grounds of religion, be excluded from participation in, be denied the benefits
of, or be subjected to discrimination, to include sexual harassment, under any program or activity supported by state
andlor federal funds.
15. Environmental Tobacco Smoke. Public Law 103-227, also known as the Pro-children Act of 1994 (Act), requires
that smoking not be permitted in any portion of any indoor facility owned or leased or contracted for by an entity and
used routinely or regularly for the provision of health, child care, early childhood development services, education or
Hbrary services to children under the age of 18, if the services are funded by federal programs either directly or
through state or local governments, by federal grant, contract, loan or loan guarantee. The law also applies to
children's setvices that are provided in indoor facilities that are constructed, operated, or maintained with such
Federal funds.
The law does not apply to children's services provided in private residences; portions of facilities used for inpatient
drug or alcohol treatment; service providers whose-sole source of applicable federal funds is Medicare or Medicaid;
or facilities where Women, Infants, & Children (WIC) coupons are redeemed.
Failure to comply with the provisions of the law may result in the imposition of a civil monetary penalty of up to
$1,000 for each violation and/or the imposition ofan administrative compliance order on the responsible entity.
Contractors are prohibited from promoting the use oftobacco products for all clients. Facilities supported by state
and federal funds are prohibited from making tobacco products available to minors.
Attachment F - RevisedAHS -12-08-09
- 25-
�Attachment G - Service Level Agreement
PUBLIC COMMUNICATIONS SERVICES, INC. (PCS)
pes Service Policies &
Procedures
For the Vermont Department of Corrections
pes
�Attachment G - Service Level Agreement
Service Policies and Procedures
Introduction
Public Communications Services, Inc. (PCS), is in the business of connecting inmates
to their families and friends while providing premier investigative and monitoring
tools for use in the secure corrections environment. PCS principals have specialized
in inmate communication systelIls for more than 20 years, a focus and commitment
that few companies in the nation can demonstrate.
Approach
Our continuing mission is to be the premier provider of inmate telecommunication
systems and related services through exceptional quality in both service and
operations.
PCS accomplishes this by providing the VTDOC with Site Administrators and
technicians and aligning PCS's Technical Services Support Staff into a multi-tier
support structure to ensure that they strictly adhere to our quality, service and
support standards. These elements allow for immediate support and remediation of
Service Events, 24 hours a day, 365 days a year, that may be reported to PCS via the
following.
•
•
•
On-site support personnel;
PCS's BMC Service Desk Express trouble reporting system;
PCS's Technical Support number (800) 6-INMATE (a.k.a. (800) 646-6283)
PCS also maintains pre-defined Quality Management, Change Management and
Service Level Management (SLM) programs to ensure we provide the highest quality
of service and support to our customers. SLM is one of the core ITIL version 2 and
version 3 principles focused on providing the premier service quality by aligning how
PCS works to the services we provide. This, in turn, supports our commitment to
~ ensuring that customer issues (we call them "Service Events") are resolved on time,
per our internal standards and contractual service level agreements (SLAs).
These practices form the core of PCS's operating philosophy, and are the basis of our
quality processes for everyday practical use. Following these practices requires, on a
regular and ongoing basis:
•
•
•
2
Authentication of established service levels;
Highly visible reporting of results, positive or negative;
Quantified, measurable, meaningful metrics for break/fix;
�Attachment G - Service Level Agreement
Service Policies and Procedures
•
•
Gi1>;·pcs
Puhtic ('.<.numunkJflon~
$cr~",
Willingness to change the scope, form, or support levels to meet SLAs, as
business needs evolve; and
A serious commitment to a meaningful Total Quality Management (TQM)
process.
It moreover must be recognized that when expectations and quality commitments are
not established, it is generally very difficult to satisfy the service needs of the
Operations Division and our customers. Thus, PCS's operating practices represent our
means of establishing and adhering to a set of expectations that are realistic and
achievable, all to meet our ultimate goal of having satisfied customers.
Preventative Maintenance
The key to system reliability is preventive maintenance. PCS Field Services
Technicians visit the facility on a regularly scheduled basis and make contact with key
facility personnel to address any new concerns. Each regular visit will include the
following:
1. Physical test of all inmate phones for functionality including voice prompts,
keypad operation, and handset operation. Test all outbound trunks for dial tone
and proper PIC code. Complete all required inmate phone repairs.
2. Operational test of all call processing equipment and perform routine
maintenance and cleaning.
3. Verification that all new facility personnel who work with the inmate phone
. system are familiar with the proper operation of the system and provide training
as necessary.
4. Verification that the appropriate facility personnel have repair and technical
service escalation materials.
After every visit, technicians will complete a PCS Scheduled Maintenance & Service
Form that is forwarded to PCS for Technical Services to evaluate and track.
Emergency Mai.ntenance
Anytime a client reports a problem, our experienced Technical Service
Representatives will respond within 30 minutes. The Technical Services Department
receives inmate phone service calls from facilities across the nation, ranging from
State Departments of Corrections, CountY SherifFs Departments, Immigration
Detention Centers and City Jails. The facilities contact us via a 24-hour live-answered
number: 800-6-INMATE.
�Attachment G - Service Level Agreement
Once a problem has been reported to pes, Technical Services staff will create a
trouble ticket and begin remote. diagnostics. If the problem cannot be fixed remotely,
Technical Services will arrange for a factory-trained field services technician to go to
the facility to make the repair. pes will adhere to the following protocol when
responding to a request for technical support.
1. When the facility site contacts pes via the 800-6-INMATE line, a ticket will be
opened and a phone call put through to a backup technician.
2. The backup technician will report their status and provide an ETA.
3. A pes Technical Services representative will contact the person who has
requested dispatch to let them know the ticket number and provide an ETA for the
technician en route.
4. The technician will notij'y the pes Technical Services rep. when they have arrived
onsite; will sign the facility check-in form on arrival, and meet with the escort
provided by the facility (if available/required).
5. The technician will report the status of the issue to pes if they are unable to
resolve the problem immediately.
6. The pes representative will·contact the VTDoe staff member who reported the
problem, and provide them with a status report of the situation every hour until
resolution.
7. The Technician will notij'y the pes representative of ticket completion if they are
able to resolve the issue.
8. The pes representative will contact the VTDoe staff member who reported the
problem to let them know that the problem has been resolved. If they are satisfied
with the resolution, the tickf~t will be closed.
4
�Attachment G - Service Level Agreement
Service Policies and Procedures
iii:
"
',-
-,-~"---,,'
I' ;~~R'cieateSH3- i
iL>FacilitftiiftS:: _ [
trduble:iicker .
'i"aoo-silNMATE .i
~p~;!:
I
_-.c~~,---c.J
r~·~sTi;~~
I
fS[~T~;
I.·~
If unable to
repai,' remotelY,
lechnician is
otspatche(HO
\ lacHity~1g_~ep#;,-'
I -,,'
,",c ,:: ,'h,< _ -"""
··1
A
I
~rszJ
"tj
'j
_;11
'..,Mlelan
~i
I ,: ,and notifres,
'
I
I completes r:ePflJt~i
\i
~:?~~I~~;ftaf(
iFacility is notified
! pf resoJutfon ¥a
ii
pt\one~or,_email:
I;····>·····
.
, ..
r'
Service Event Tracking and Life Cycle
Each Service Event, whether a reactive break/fix scenario or a proactive change
request, is logged and monitored through PCS's automated Ticketing System. PCS's
Ticketing System tracks Service Events, assignments, escalations, and response and
resolution times for each Service Event, from its initial entry to final close-out. The
Ticketing System monitors incidents submitted through any means, such as
automated monitoring system alerts, a phone call from facility staff, technicians or
site administrators, e-mail, fax, or inmate complaint form.
The system also supports automated notifications and escalations based on response
and resolution business rules established per priority, by facility. Each Service Event
Ticket moreover is assigned to an individual owner who is responsible for tracking
and ensuring that the issue is remediated to your expectations and within the time
frames of the Service Event's priority level.
On the following page, you will see a diagram of PCS's technical support Service
Event Life Cycle.
�Attachment G - Service Level Agreement
r'''!;~pcs
Public ComrnU:'lili."1I.tiom;
Service Policies and Procedures
Ser~8
Service Event Life Cycle
Level 1
Customer:
Problem
IdentifICation
SyS!l1m'
L 1: ClOsing
l1: Service
EvMt
RemooialJon
Priority One
L1:
Incident
C-.d
S"'""'
! Escslatlon to
L1 :
an Incident
&C,ien(
1 NGtiflcahon
I Pr~rQ
Procedure
L2
L..L_ _ _-'-.J
No
Level 2
L2
L2: Service
Event
Remediation
Procedure
Re-prioritize
Wo<kLD""
.. new
ServfeQ event
ySle
Has alloWed
L2: Incident
trouble shooting )--NI""-< Resolv3d?
time
,,..,
L2: Closing
an Incident
Yes
-----------------_. --------------------------.- ----------------------
Level3
,
,
I
I
LJ
Pre.priofl!lZ$
I
1.3: Service
E"en!
\NtJ.rk load fur
RemediatIOn
Procedure
new Service
Even!
ystem.
as allowed "
trouble shooting '::-N
lime
/"
Yes
l3: Active
SWAT
Remediation
Pnx:&ss
I
Service EV€"nt ~
I
I Management,
I
E!:i: to: ).....----""
I
Sy&iem; Auto-Notlficatkm of VP, Directors, aJ'ld
Managers.at periodic milestones oj'the
remaming
ETA time based on the service evem's priority
6
Prowdu~~J
L3: Clos[ng
an Incident
�Attachment G - Service Level Agreement
Service Policies and Procedures
~·"'~PCS
Service Event Priority and Remediation
pes is cDmmitted tD the prompt repair and/ Dr service restDratiDn .of inmate telephDny
services in the unlikely event .of a service interrupti .on, as well as to res Diving any
service request properly and .on time. AccDrdingly, pes has established standards fDr
.our respDnse and repair times, tD which we rigDrously hDld ourselves.
The fDllowing are pes's standard service levels and resDlution times:
;?"\I~?. q~~~t~n~f(p~~I1~. p.
PI
P2
P3
P4
PriDrity Level I items
are major Service
Events that globally or
severely impact the
ability .of inmates tD
make telephDne calls
or .other services.
Priority Level 2 items
are Service Events
impacting an entire
hDusing area and that
require immedi'lte
attention
Priority Level 3 items
are basic service
requests fDr min Dr,
nDn-critical incidents.
PriDrity Level 4 items
are lower priority
requests that that dD
nDt directly affect the
availability .of services.
·Itxil.mple$
. .•... • .<
.;;.
.c~~1;g~~'sM .
• Entire system fails
• Multiple entire housing areas
not DperatiDnal
8 hour physical
respDnse and/or
remDte reset;
Repair made
within 24 hDurs
• One entire housing unit nDt
DperatiDnal
Repair made in
24 hDurS
• One Dr more inmate phDnes
in a housing unit is not
DperatiDnal
Repair made
within 48 hDurs
• DevelDpment .of new features,
report creatiDn.
As mutually
agreed upon
with facility
persDnnel.
In certain extenuating circumstances .outside .of pes's cDntrol, such as events of FDrce
Majeure, the fDregDing time frames dD not apply.
7
�Attachment G - Service Level Agreement
Escalation Procedure
As outlined in the Service Event Life Cycle, PCS's Ticketing System automatically escalates the
ticket for a Service Event to the next appropriate level of technical support for remediation, if
the allotted trouble shooting time has passed. This ensures that the most qualified and
available technician is working on the Service Event and the issue is resolved per our service
levels.
In order to ensure that the VTDOC receives the highest quality of service available, PCS
maintains detailed, tiered escalation procedures. PCS's internal tracking and escalation
procedures are as follows:
PCS INCIDENT INTERNAL ESCALATION PROCEDURES
Vermont Department of Corrections
1
Initial Incident
Created
2
First breach of
internal
allotted trouble
shooting time
3
4
Final
Tier
8
of internal
allotted trouble
time
Third breach of
internal
allotted trouble
shooting time
Final breach of
allotted trouble
shooting time
Levell Tech. Incident Owner
Levell Tech. Incident Owner
Technical Services Lead
Incident Number
Provided to VTDOC
Provide VTDOC a Status
Update of the issue and,
if available, proposed
time frame for
Levell Tech. Incident Owner
Technical Services Manager
VTDOC a Status
Update ofthe issue and
time frame from
Services Manager
Director of Inmate Support
Operations
Additional Operations Managers
(as needed for SWAT process
Provide VTDOC a Status
Update of the issue and
revised time frame from
remediation
Technical Services Manager
Director of Inmate Support
Operations
Vice President, Operations
Technical Services
Manager, Director of
Inmate Support
Operations & the Vice
President of Operations
will personally oversee
the remediation of the
issue and the client
communications
�Attachment G - Service Level Agreement
Service Policies and Procedures
Moreover, in order to ensure direct lines of communication between the VTDOC and PCS, we
have developed the following communication escalation process available to the VTDOC, if in
the rare instance, VTDOC personnel do not find that an issue is being resolved to their
satisfaction:
COMMUNICATION ESCALATION PROCESS
Vermont Department of Corrections
1
2
3
4
Final
Tier
or
One Hour Past the Required Repair
Timeline
Second Call or
Two Hours Past the Required Repair
or
Three Hours Past the Required Repair
Timeline
Fourth Call or
Four Hours Past the Required Repair
Fifth Call or
Five Hours Past the Required Repair
Timeline
Technical Services On-Call: (424) 202-1957
Direct Line: (818) 898-3584 Or (800) 646-6283
Technical Services Lead:
Lori Floyd (310) 220-9893
Technical Services Manager:
Matt McFalls (817) 491-5163
Director of Inmate Support Operations:
George McNitt (817) 690-4809
Vice President, Operations:
Doyle Schaefers
000 x3027
Issue, Trends, Problem Identification Tools
PCS uses an array of tools to help identify issues, trends and potential problems. One
common tool is the PCS's Ticketing System reports, which prOVide a summary view of Service
Events, their respective priority levels, their occurrences, and our adherence to service levels.
To ensure complete client satisfaction and visibility, these reports are available to our clients
as requested.
PCS also employs remote network monitoring systems Big Brother, Solar Winds and
Scrutinizer. Big Brother identifies potential issues in MPLSjPIP (Proprietary Internet
Protocol) and WAN connectivity. With this software our Technical Services Department can
remotely monitor processor load, disk and memory usage, log files and currently running
processes on client's host server. We can also check environmental factors such as
temperature that might affect system function or durability thus proactively preventing
problems and maximizing system uptime and functionality.
As an extra monitoring tool, PCS monitors all network devices throughout the United States
using Solar Winds. Solar Winds provides event notification, event logs and the ability to
combine measurements from connected devices to drill-down within systems and identify
which component within a local network is having problems. This enables PCS's Network
Operations centers to be sure they are dispatching the right technician with the right tools
9
�Attachment G - Service Level Agreement
Service Policies and Procedures
and equipment for each repair leading to prompt resolution of any issues detected on PCS's
network.
In the event that a problem is detected, often before any service disruption can occur, Big
Brother automatically sends a notification to PCS Technical Services and to the client server
and local technician. The client can be notified by email, pager or other preferred method.
To monitor the traffic load on network links, pes uses the Scrutinizer NetFlow & sFlow
Analyzer software. Scrutinizer retrieves traffic details from routers and switches, and reports
on the protocols of packets flowing over the routers. It provides real-time details on how
much bandwidth is being consumed on a protocols per-station and stations/hosts per
protocol, and presents them graphically. It can measure the volume and rate offlow of traffic
through every router on the pes WAN over any time period from a matter of seconds to
months and present it graphically for examination.
Site Administrators
In order to provide the highest quality and most responsive service possible, PCS will,
in addition to following the above Service Event resolution procedures, and using our
Field Services Technicians and Technical Services staff, provide VTDOC facilities with
Site Administrators. These Site Administrators will be present to take responsibility
for database and account maintenance and also to help the VTDOC's staff take
advantage of our system's full capabilities. PCS will provide Site Administrators who
meet the VTDOC's specifications and are approved by the VTDOC.
PCS's Site Administrator position monitors the overall operations of the inmate
telephone system, is prepared to testify as to chain of custody of call data and
recordings, performs data entry, responds to requests and complaints from both
facility personnel and the inmate population, and arranges for repair of on-site
equipment as necessary. The Site Administrator is your first point of contact for any
questions, concerns, or reports regarding the inmate telephone system.
Site Administrators also may take over tasks currently being performed by staff
members, and help to optimize system benefits, such as monitoring calls to alert staff
of a security breach and reporting three-way call attempts. Site Administrators work
directly with our maintenance and service subcontractor and with PCS internal·
Technical and Field Services staff to proactively identify any service issues and ensure
Service Events are reported and resolved in a timely manner, to the satisfaction of
facility personnel.
Problem Management
Problem management, an essential core function of a comprehensive service
program, focuses on identifying the root cause of service problems as they arise.
]0
�Attachment G - 8eJvice Level Agreement
Service Policies and Procedures
PCS's problem management process encompasses regular meetings and
system/network performance reviews. First, PCS operations and technical staff
review Service Events during our weekly technical service support team meeting. As
needed, additional conference calls with the appropriate support personnel and
associated contractors are held to ensure events receive the most complete analysis.
Second, Quality Control leads a monthly incident management meeting. The purpose
of this meeting is to discuss recent issues and any trends related to system support
and system reliability. Attendees include, but are not limited to, personnel from
Technical Services, Network Engineering, Field Services, Project Management, and
Operations Senior Management.
Root Cause Analysis
pcs has a rigorous root cause analysis program stemming from our dedication to excellent
service quality. We work to ideritify the root cause of problems by analyzing related
incidents, if available, or through detailed system/network research. Once we identify the
root cause of a problem, we determine and implement preventative process changes and/or
solutions for long term remediation, which are documented on an internal change request
form, and handled by Quality Control through the change management process.
Change Management
pcs adheres to a change management process to ensure that all changes introduced
into production are appropriately scheduled, communicated with each facility
representative, and carried out. At a high-level, changes are entered into PCS's
Ticketing System. These changes are reviewed by our internal Change Advisory
Board (CAB) for impacts, risks, and scheduled release date approval. The review also
incorporates analysis of any pertinent documentation, such as a high-level
requirements summary, system impact analysis, unit testing, or detailed testing
results.
Once approved for scheduled release by the CAB, the release date is confirmed with
each affected facility to ensure no service or other adverse impacts to the facility will
occur. A separate release notice is sent out to each impacted facility and to internal
PCS personnel. The changes are then made to the production services, network,
servicer, or systems, re-tested to confirm adherence to requirements, and, finally,
certified as production stable.
Note: Large system changes are treated as a Project and thus follow a more rigorous
Project Management Process. The change management process is but one component
of PCS's operating procedures for large project management.
�Attachment G - Service Level Agreement
Service Policies and Procedures
~~~
Quality Control
Quality, in all aspects of our operations, is one of the most important factors for our
continued success in the day-to-day performance of our contract. Whether it's in the
products proposed or the services selected, PCS strives to ensure that all expectations
of the VTDOC are met or exceeded.
As evidence of our commitment to quality, pes established a formal quality control
(QC) department in 2008. Our QC Department uses the latest testing techniques from
various industry quality standards, such as ITlL, TQM, Lean Six Sigma, and TL9000, to
ensure PCS continues to meet or exceed customer expectations related to service
quality. In particular, PCS uses a combination of manual, automated, semi-automated
techniques looking at functionality, features, performance, network, and pre- and
post-service quality validation. The QC team is also responsible for testing, root cause
analysis, service level and change management; however, their primary function is to
ensure PCS meets our quality standards.
At PCS, quality has been built into the processes by which we provide and implement
service, thereby aligning how we work with the services we provide. Testing is
typically managed internally by PCS staff and has been integrated within our business
processes. Thus, in some cases, the QC team performs an over-site/governance role
by which they ensure the appropriate testing steps are being followed, and they
conduct an independent review of the results to ensure we are meeting our goals.
In so doing, PCS's QC team uses different methods to certify the quality of the
telephony services being provided. The following summarizes, at a high-level, some
of the techniques used to meetthese objectives, together with a description of how
the quality objectives are met per component:
CompoIl~!lf.
L:.·.> .•... <... .
pes's Quality
Assurance
Framework
Quality Control
Processes
12
fhii.
.•.•. It~mpdnent~etalI~ ' . F ' •.. •. . ;
R61es involveH
If<ls<l .
r{<ltef..
pes's quality assurance framework (QAF)
See roles listed in
provides detailed gUidance on PCS's quality the Program
methodology. The QAF includes four main
Management
components: quality control processes and Section of the
quality control reporting, quality control
QAF document.
infrastructure/resources, and quality
management.
Quality control processes are the
See roles listed in
methodologies and techniques used to
the Program
support pes's corporate quality objectives.
Management
Section of the
QAF document.
> ...••
�Attachment G - Service Level Agreement
Service Policies and Procedures
Quality Control
Reporting
Quality control reporting is the various
system monitoring or trend analysis reports
which provide a visual method for
monitoring and measuring all aspects of
Quality Control
IT &Ops
Development
Ops Network
Quality Control
Infrastructure/
Resources
Quality control infrastructure/ resources
include the tools, environments, QA lab,
servers; people, and any additional
equipment necessary to support the quality
Quality Control
Operations
Defect Tracking
Error/defect tracking is covered under the
quality assurance framework. PCS uses an
industry-standard defect tracking tool and
lessons learned sessions to capture, identify
and enforce our change management
processes related to quality assurance work
flow.
Standard system testing (such as unit
testing, regression testing, user acceptance
testing, feature/functionality testing, etc.) is
for ICM
Rate validation testing is
the rate change "goes live" and after the
of the rate into
Call detail reports are system-generated
reports which itemize all call related details,
such as BTN called, date and time each call
was made, inmate PIN, cost of call, was the
call
call
During new
implementation and/or
major facility changes such as a service
conversion, PCS's network engineers, field
services specialists, and project managers
complete post-implementation testing. The
results of this testing are captured in the
Post Implementation Test Plan.
Appropriate preventative measures and/or
pre-install improvement testing techniques
are also
as
The Backup and Recovery Procedure
defines the standard operating procedure
and detailed work instructions needed to
ensure that critical
Quality Control
Project
Management
Engineering
ICM Features and
Functions
Rate Testing
Call Detail
Reports (CDRs)
Post
Implementation
Testing
Backup and
Recovery
Procedure
Development
Quality Control
Billing Operations
Quality Control
ICM
Billing Operations
Quality Control
Field Services
Reps
Project Managers
Network
Engineers
Quality Control
Technical
Services
Representatives
~_M"===_'_,~··~_
13
rI
�Attachment G - Service Level Agreement
Service Policies and Procedures
~olllPonent
I> .• '
............. . COmp()nentDetalis
.....
. ....
Site
Infrastructure
and Network
Drawings
Project
Documentation
Pre-Installation
Testing
ITS
Implementation
Standard
Operating
Procedures (SOP)
14
.....
.
,.
. ...
Roles Involved
...
. f'ls<!l1llfoflrhltel·'
system configurations to call data, is backed Support
up appropriately.
Project Managers produce a site
Project Manager
infrastructure diagram, often referred to as
a "network drawing." This provides a visual
representation of a site's hardware and
network configuration. The drawing
includes the customer's facilities, the inmate
phone systems, the circuits, bandwidth
allocations, how each site is connected to
the host, how the host sites are connected to
PCS, etc.
Project Managers create and maintain
Project Manager
various project documents which are used
Documentation
Team
for maint;lining project tracking, cost
control, and project oversight The
following are some examples of project
documents: an MS project plan, an
implementation plan (also known as an
installation plan), a statement of work, a
contracts deliverables checklist, risk
registry, cost documents, project charter,
user manuals, and training documents.
Pre-installation testing includes both unit
Engineering
testing and system testing of the inmate
Quality Control
telephone system, hardware, software,
connectivity, call and prompt quality, within
the test lab.
The ITS Implementation Standard Operating Project Manager
Procedures provides guidelines for the
ITS
project operations team in the initiation,
Implementation
planning; execution, monitoring, and closing Standard
of inmate telephone systems
Operating
implementations. One element of the SOP is Procedures (SOP)
the verification of contract deliverables
under which the Project Manager confirms
that all of the proposed project deliverables
(such as setup and equipment) will meet the
contract compliance requirements.
..
....
�Att,achment G - Service Level Agreement
Service Policies and Procedures
Conclusion
Quality and service are two of PCS's core success factors embedded throughout PCS's
service delivery model. Though quality is baked into our overall process, we also
continuously monitor and review our quality processes to verify that tbey are meeting
our objectives and being followed. Using a combination of Service Level Management,
Change Control, Project, Problem and Quality Management techniques, PCS is able to
ensure the integrity of our service and day-to-day business operations. Our Quality
Control team also functions in a proactive fashion, looking for possible issues, trends,
and uncovering the root cause of issues to prevent potential long term problems.
With our comprehensive approach, PCS is able to offer you, our customer, premier
inmate telecommunications services grounded in exceptional quality of systems and
service.
�Attachment H
10
I
.
Task Name
Finish! Calander Days LY-tQ~-'1.Q-r"T-L~"~~,~1Q_,,_."., .Mp,Y,
Start
:=r"trct~~~~a:.r:o:;:~~::~r~~:::·~~::::~::r~:e· ..~~"~""~~""""~"""~~ ..~M~~~~~%~~i"~"Fr~~i~i1~~~~~"42~:!~d:F~t~lJJWJI E. L~."MLI. WlTlfI~ 1~.lM!
'j
2
3 .".!
~4--1
·..
Initiating Phase
Contract Award from State of Vermont DOC stakeho!ders
}~]
~~~~r:~~~~I~V:~~~;:~'6~;;!~~Ved
"'~ ... -j
10
.-!
1i.·."21':'.·:~jJ
•.·.·.·.."..
" "____
"~~"I
-15'-1
25
26
":3'281"=1!
~"t~~J
3Lj
34
35··
···36
37"1
"38]
'th'Li"10)7116'
1 day
:~i ~~;:;~~i~~i;~~;~~
~ ::~I
2 days
~:~ ~ ~;~ ~;~ ~l
~~: ~ ~;'~. ~;~~'
21?;;,~1
wed -fbl'f3/101""
Wed 10d3/10'
1 day]
Update Sophia
Compiete 'con'iigu'rafi'o'il"and ordering workbook
Doc'lj'me'rli'dat'a upgrade/trans'fer -project scope
Backoffice "Setup"'Phiii's'e"'j''''Com plete
Ordering
Order hardware for facilities
Order/ print postings
Ordering C'ompfete
Configuration and testing phase
Action items complete
bat'ab~ls'e"coiifig·u'i-ation complete
Development items compiete
b8:'tabase confl'guration -lab' tes'fing "C'o'mp'lete
Hardware rece-iveej"'(il" b'iii'r'las" '"
Hardware configured
Hardware tested in lab
.... ··rfi'Li"·ibi14f10'
fda'yj
Fri 10/15/10,
31~: ::~:
Man 10!1Si10:
Man 10/18/10;
::: ::;:~;:~
1 day
Man 10/18/10
M(iil'''1'6h'si1"0
0.25 days
0.13 days
Wed 10113/1°1
Wed 11110110
Man 10118/101
Man 10/18/101
Man 10/1's/1"6:'"
Man 10/25/10]'""
Mori"10/2'S/1'ijT'"
Mon'10i:2Sl1o!
Man 10/25/10
Fri 11/5110'
Thu 10/7/10:
Man 10/18/101
Mon'10/2"5H61
Tue 10119/10
Thu1017l10!
."...1".
:..: .....:..:.:.:...............................
Split
Thu 10/14/101
Fri 1065i1oi
W!~U1~~;;;:~! .
Hold Kick~offmeeting
Task
Project: Project Plan
Date: Fri 9/10/10
Thu 10/7/10]
:~:~::: ~~:~:~: :~:~:rcreated
Plan~~:k:;~:eSetup Phase I
···24·
Tue 10/5/101
p'roject 8:ssign'iTi'enffo"p'ro)Ei'ci'iTianager
Circuit upgrade request'pTiiced''''
Initiating Complete
16
"'1-':1"
23
10.25 daysl
1 day
~on 10/~,/101
initia'i nE;tWo'rk~"'!in'd"hlirdWiire'''co'ri'figurati'on 'documented and approved
iiiit'ial 6udge'i"es'timat'e documented and" approved
l
·'··'·~rm'·'...
Thu 10/14/10
Man 10/4/10
Wed 10/6/10'
Man 10/4/10'
J
lwlW
Milestone
Summary
.
;;
Progress
Page 1
.
f.Acl'il""f6J2SHo'
Vi/ed-10iio/1-0;
f.:j1Oil"·10/25/10
FrI1-1i5i10~
Thu 10/28/10'
"'""Fri'11/5/10
Fri"1'1"'Jshb
Thu 11/4110
"fh'u'''f6i2'1i10
Thu 10/28/10
Wed 10120110
26
daYSi
1 day
6.43 days
2 days
() ei'a}'-SI
10.25 daysl
3 days
~:.1~::1
..
~"~:~:I
l
125days
Thu 10/28/10!
:
Thu 10/28/101
Fei 10129110
""Wed '"1"1'i3/1 0
5.25 days'l
11/3110'
Thu 1114110
Thu 11/4110.
1 da~J
Wed 1113110:
Wed
....•...................
;;
External Tasks
~
External Milestone
~
1 dayl
1 day!
":_"':' '''''((,,:_>,:kX'
'
�Attachment H
ID
Task Name
"""""- -Con'rTgu"i-'iiiiOn"'ancftesting-phase'·complete ..""---""".--,. . ---.,-...-,.......-----,--..----,-.----,-"--","-'" ___",_"l ..
:i9~
40'''42~
4T"
Wed 1111.0/10;
5 days
Th'u'1'1/4H6"
f'd'T1isJ1'b"
0.75' days
Forward shipping info to PM and receiving party
'fh'u"f1'i4Hoj""
'6 days
Wei'if1'1h'oho
Wed 11/10/10
o days
Pre-Installation Phase
iil'ventory
~~,d, 11,~,~,~!~,~L
Fri 11/12/10
2 days
2' days
Customer update
~1.·~.~"jJ
4.25 days
Wed 11/10/10:
E'qulpm"enf
:~
0.75 days
Wed 11/10/10
Wect-'1'iHoifo:
Shipping Phase Complete
-46~'J
F'if1"1'iS/1'O"
Fri 11/5/10;
Planning Complete
44
'~~53-"
Thu 11/4110:
Verify delivery
45
TShtau'_'~l' 1/~4'1'1· ·0'-,'.' ,-.---~iT~hi~u~-11-/4··/~1·0"·1·--:~~-~·~-~~-:·'~0'~d-'~aSy···s,)~it1w~IIEJg; :~~IT1~&IEI$_.,~I~J
Packa'£Je '8:nifsh'ip hardware
Shipping phase
4'{
",,0, -
55
-'56
Frl11/19/10:
-Reno'\/o/"r;.j'jixkjja"ira·lnlng'
Man 11/15110;
Man 11/15/10:
Tue 11/16110
Tue 11116/10'
E'qui'pm"enTTils'iiiiTa'iki'iiFtesting ~ PCS
Man 11/15/10i
Tue"'1"1i1'ei1b;
System Testing 1 Cutover - PCS IShawntech
Man 11/15/10;
"Tue"f1'I1'i3Ho i
Tue 11/16/10
Wed 11/17/10
Tue 11/16/10'
Wed 11/17110'
wedi1ii7/10 1
Wed 11/17110:
1 dayl
1 day!
Wed 11/17/10
Fri 11/19110;
Thu 11118/10;
2 days!
1 dayi
Thu 11/18110'
Frf"f1'/1's/fo'!,
Thu 11f18/10'
, F'j{"fi719/1ci"
1 day~
'i'd'ayl
Northern State
-"[;T'
Renovol Nexidia training
58-
Equipment Installationl testing
-59~"
"~65""
~
Tue 11/16/10~
PCS
System Testing I Cutover - pes IShawntech
Tue 11/16/10
Northeast Regional
""sT"
--62
Wed 11/17/10
Renovof Nexidia training
Equjpm'j3'nt"fnstaTiaiki'nl"testl'ng"'~"'pes
'sr
System 'iE;stfiiii'j"Cutove'r"~
'PC'S IShawntech
Team-2:
64
-'65~"i""""""""""""""
Northwest State
"~6ir~
--6="-""'68'""
-69-
io
73
Project: Project Plan
Date: Fri 9/10/10
,
4.5 daYSI
4.5 da""l
1"day!
1 day
1 daYj
1 daYi
1.5 days!
1 day!
,
:3 daysj
Mon 1-1/15110'
iiiulilitiiiii
Men '1' 1h566;
" 'Tue"11/161101
,
TueiihSiiO ,
1 day]
1 day;
Renovol Nexidia training
Man 11f15/10'
EqUipment Installationl testing - pes
Mon 11/15/10
Tua 11116/10
1 day!
System Testing 1,Cutover ~ PCS IShawntech
Man 11/15/10
1 day!
,
Tue 11116/10
Tue 11/16/10;
Thu l11isll0:
" Tue 11/16110""
wed hi17f10:
2 days\
1'day!
Equipment Installation I testlng~ PCS
Wed"1' 1t1'iiio"
... Thuii/18/10
1 day1
System Testing I Cutover ~ PCS IShawntech
Wed 11/17/10'
Thu 11/18f10;
M'on'1'1i1"5/1"0"
..... '1',111119/10;
Chittenden Reglonal
Renovo! Nexidia training
7T
"72-
2 days
o days
iVI'o'n"1"1i1Si10!
........................................ .
Caladonla Community Work Camp
~~E:J
Fri 11/12110
Mon 11/15/101
Installation Phase
.
F'ri"1'ihiNo"
Wed 11/10/10 1
Fri 11/121101
Fr; 11/12110
Fr; 11119110:
Pre-Installation Phase Complete
Team 1
Wed 11/10/10~
Team 3
Task
Milestone
Split
Summary
External Tasks
.Ol""---"'-~::;;
Progress
Page 2
External Milestone.
1 daYj
4 days,
�Attachment H
ID
ITask Name
-.:.~7·••.~6-.-.-..-j· ".,----,._. . __.- '---sout~:~:~~i~~Xid ia -t';:~~'i-:~-'-------'-'-----'
_.- . ",,---". _. -,---".,.~.--.,. --'"-,-.--.-,-"--~~-. ~-",.-.--'
_ __ _
E'quipment Installation ,-tesHn'g:"'fj'CS'
"T!" . j
System Testing (C'Lj'tover'''~''p'(::S /S'hawntech
78 . ..1
... ·'8·0'·..·
'"'''8T''~
System Testing I Cutover - PCS IShawntech
aX--
Marble Valley Regional
Renovol Nexidia tra'ii-li'ng'"
83
Equipment Installation! testing ~
pes
Installation Phase Complete
-rue 11/16110:
~ d,8Yi
1 day.
Man 11/15/10
Tue:--1'1li"EiH6t
1 day
~~:::;::;:~[
,
,,~~_"
Thu-11h'sh"oi'"
1 daY
Wed 11/17/10
Thu 1111811if
Thu 11/18/10.
Fri 11/19/10 1
t dayl
Thu 11/18/10
Fri11/19/10:
11119/10
Fri 11/19/101
Fri 11/19/10
l
' ••••••• "
--,-dayl
~'r:~~;~:;~~t
Fri 11/19/10\
.. .....
1dayl
0 daysl
. . ~·;~~:~1
0 daysl
___ ._,_ •• ,_ •• ,_. ___ ." _ _ -'--,, ___ ,_ _ _ •____ ,:J~_~,
Split
Summary
Iij$......_--OIijfJ
External Milestone
Project Summary
:¢'"a~~_~--~-~-~-=",v
Deadline
External Tasks
Page 3
1
Fri 11/19/101
1 dayi
Fri 11/19/10,1 dayl
Milestone
"''''',','''"''''
day!
-'Wed 11/17/10
__ •__ W_" _ _ _ ~. ___ . _ . __ •_ _ "~,,~
.
~:;~I
Wed 11/17/10[
Task
Progress
2
-fue"'HhS/10
~:: ~~;~:;~~
Closing Phase
. cii'stomer sign.:citf' ~lnd acceptance
~.....
Tue 11/16/10;
Man 11/15/10,
fhulli1S/10
Thu 11/18/10
System 'testing I Cutover ~ -PC'S''IShei'wntech
Project: Project Plan
Date: Fri 9/10/10
Finish .______ _Calander
Days tMl.I
~Y-19i"~~iL'-I-.';Mi!Y'.~t;'Q~----1IMay,
__________
_____________
.•\f\IJJJ£. _~_i$_lM1TJyJ1T.LE1.__.J",I
Mon 11/15/10
~:: ::;::;:~
Southern State
R'eriovo! Nexidia training
Equipment Installation! testing ~ PCS
.... is
J
__ .. ~.t
_ _....
......a. rt.._........
.__
iP
__
�Attachment I
CommissarylInmate Accounting System Project Plan Timeline
Vernwnt DOC inmate Banking / Commissary I Secure Deposits High Level
imnlementution Plan
October
Begin
lOll
IVtilestone
Particivants
Ion
First
implementation
meeting
foUo\.\olng
completed
contract
VT
pes
x
x
x
x
x
x
x
x
x
Delivery and
configuration of
Equipment and related
network/infrastructure
Services
x
x
x
End
Plan Review j
Project
Kickoff
Prior
Vendor
Keefe
Outcome
Description
Review/Confirmation
of Preliminary Projecl
Milestones, Detenninc
Prqject participants J
DOC
roles
Detennination of
c-Olifigumble items
slIch as chart of
accounts, Bank
intormation, High
Level lnterfaces,
Authorized Users,
1014
]017
OverY iew and
Configuration
Specifications
Introduction and
debit release, phone
demonstration of
system features
IVR, direct debit,
online deposit profile,
network, user
interface, data
migration, marketing
materials for online
deposits. phone direct
debit, web product
sales
Detailed Interface
Specifications vVitil
t017
]Om
Design
Specifications
Finalization of
design::; for
configuration
(md engi,neering
Procurement of
Servers,
Software,
Projected Timelines ~
Presentation of
prototype system with
all configurable
attributes set per VT
DOC specifications
lO!8
IOil5
Provisioning
lon3
10120
Interface
Development
Coding J?nd
Testing of
Interfaces
Completed Interfaces
x
]0121
10/22
Data
Migration
Sample data
migration and
presentation
Trial Run of data
migration plan \'VillI
sample reconciliation
x
telephony
equipment,
rntL~et circuit,
hostina services
x
x
x
�Vermont DOC Inmate Banking / Commissary / Secure Deposits High Level
Inwiementation Plan
October
Begin
Milestone
])escI:iption
Participants
Keefe
PCS
OperationnJ system
pending tinal testing
x
x
Fully functional
system and
confirmation or'golive' date
x
x
Outcome
End
Prior
Vendor
VT
DOC
Spin up of
equipment
sofu'\~dre
10/21
10!22
Installation
services,
networ~
10/25
10!25
1111
1111
IJiI
10!27
Ongoing as
needed
Ongoing as
needed
I lit
1111
System
Testing
telephony, enduser settings
End to end
testing of
tnmsactions,
interfaces,
services
StaffTnlining
End user and
administrator
Training
Jmnate
Training
Inmate Training
as needed for
telephony / kiosk
use
P'ublic
Training
Go~Live
Completion of
Training and
publication of
customized training
ollides as needed
Completion of
Training and
publication of
customized training
.guides as needed
Revie"" of
Marketing
materials as
needed for
online deposits,
web product
sales, telephone
options
Completion and
distribution of public
training! marketing
materials
Data Migration,
and inlroduction
of all services
Activation and use of
all system components
x
x
x
x
x
x
x
x
x
x
x
.